[ad_1] Feb 11, 2025Ravie LakshmananMalware / Cyber Attack Threat actors have observed the increasingly common ClickFix technique to deliver a remote access trojan named NetSupport RAT since early January 2025. NetSupport RAT, typically propagated via bogus websites and fake browser updates, grants attackers full control over the victim’s host, allowing them to monitor the device’s…
Category: Cyber News
Gcore DDoS Radar Reveals 56% YoY Increase in DDoS Attacks
[ad_1] Feb 11, 2025The Hacker NewsIoT Security / Cloud Security Gcore’s latest DDoS Radar report analyzes attack data from Q3–Q4 2024, revealing a 56% YoY rise in the total number of DDoS attacks with the largest attack peaking at a record 2 Tbps. The financial services sector saw the most dramatic increase, with a 117%…
Progress Software Patches High-Severity LoadMaster Flaws Affecting Multiple Versions
[ad_1] Feb 11, 2025Ravie LakshmananNetwork Security / Vulnerability Progress Software has addressed multiple high-severity security flaws in its LoadMaster software that could be exploited by malicious actors to execute arbitrary system commands or download any file from the system. Kemp LoadMaster is a high-performance application delivery controller (ADC) and load balancer that provides availability, scalability,…
Google Confirms Android SafetyCore Enables AI-Powered On-Device Content Classification
[ad_1] Feb 11, 2025Ravie LakshmananMobile Security / Machine Learning Google has stepped in to clarify that a newly introduced Android System SafetyCore app does not perform any client-side scanning of content. “Android provides many on-device protections that safeguard users against threats like malware, messaging spam and abuse protections, and phone scam protections, while preserving user…
4 Ways to Keep MFA From Becoming too Much of a Good Thing
[ad_1] Feb 11, 2025The Hacker NewsIT Security / Threat Protection Multi-factor authentication (MFA) has quickly become the standard for securing business accounts. Once a niche security measure, adoption is on the rise across industries. But while it’s undeniably effective at keeping bad actors out, the implementation of MFA solutions can be a tangled mess of…
Assessing the Risks Before Deployment
[ad_1] Feb 11, 2025The Hacker NewsSoftware Security / Threat Intelligence Imagine you’re considering a new car for your family. Before making a purchase, you evaluate its safety ratings, fuel efficiency, and reliability. You might even take it for a test drive to ensure it meets your needs. The same approach should be applied to software…
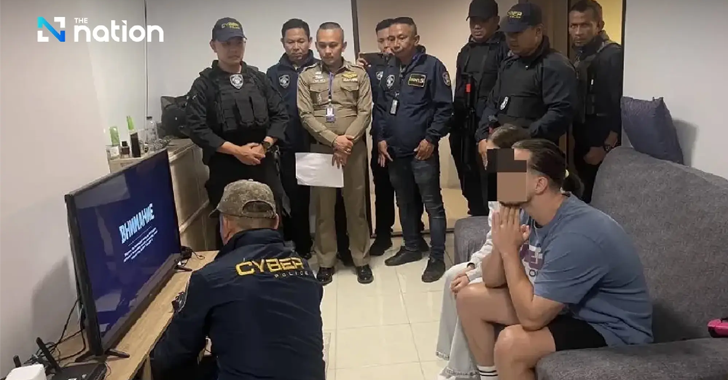
8Base Ransomware Data Leak Sites Seized in International Law Enforcement Operation
[ad_1] Feb 11, 2025Ravie LakshmananCybercrime / Ransomware Source: The Nation A coordinated law enforcement operation has taken down the dark web data leak and negotiation sites associated with the 8Base ransomware gang. Visitors to the data leak site are now greeted with a seizure banner that says: “This hidden site and the criminal content have…
Apple Patches Actively Exploited iOS Zero-Day CVE-2025-24200 in Emergency Update
[ad_1] Feb 11, 2025Ravie LakshmananZero-Day / Mobile Security Apple on Monday released out-of-band security updates to address a security flaw in iOS and iPadOS that it said has been exploited in the wild. Assigned the CVE identifier CVE-2025-24200, the vulnerability has been described as an authorization issue that could make it possible for a malicious…
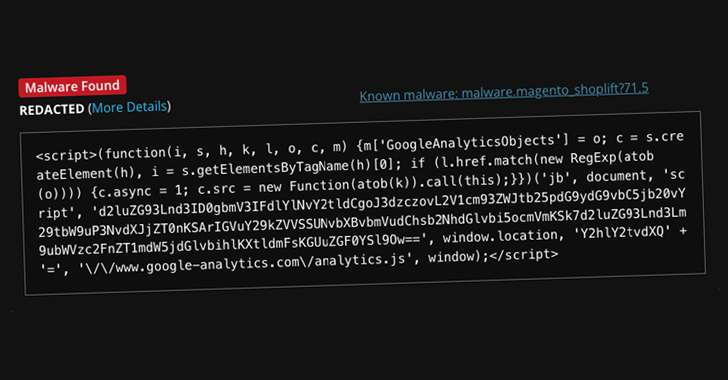
Hackers Exploit Google Tag Manager to Deploy Credit Card Skimmers on Magento Stores
[ad_1] Feb 10, 2025Ravie LakshmananMalware / Payment Security Threat actors have been observed leveraging Google Tag Manager (GTM) to deliver credit card skimmer malware targeting Magento-based e-commerce websites. Website security company Sucuri said the code, while appearing to be a typical GTM and Google Analytics script used for website analytics and advertising purposes, contains an…
Don’t Overlook These 6 Critical Okta Security Configurations
[ad_1] Feb 10, 2025The Hacker NewsIdentity Security / Data Protection Given Okta’s role as a critical part of identity infrastructure, strengthening Okta security is essential. This article covers six key Okta security settings that provide a strong starting point, along with recommendations for implementing continuous monitoring of your Okta security posture. With over 18,000 customers,…