[ad_1] Feb 01, 2025Ravie LakshmananCybercrime / Fraud Prevention U.S. and Dutch law enforcement agencies have announced that they have dismantled 39 domains and their associated servers as part of efforts to disrupt a network of online marketplaces originating from Pakistan. The action, which took place on January 29, 2025, has been codenamed Operation Heart Blocker….
Category: Cyber News
BeyondTrust Zero-Day Breach Exposed 17 SaaS Customers via Compromised API Key
[ad_1] Feb 01, 2025Ravie LakshmananVulnerability / Zero-Day BeyondTrust has revealed it completed an investigation into a recent cybersecurity incident that targeted some of the company’s Remote Support SaaS instances by making use of a compromised API key. The company said the breach involved 17 Remote Support SaaS customers and that the API key was used…
Meta Confirms Zero-Click WhatsApp Spyware Attack Targeting 90 Journalists, Activists
[ad_1] Feb 01, 2025Ravie LakshmananPrivacy / Surveillance Meta-owned WhatsApp on Friday said it disrupted a campaign that involved the use of spyware to target journalists and civil society members. The campaign, which targeted around 90 members, involved the use of spyware from an Israeli company known as Paragon Solutions. The attackers were neutralized in December…
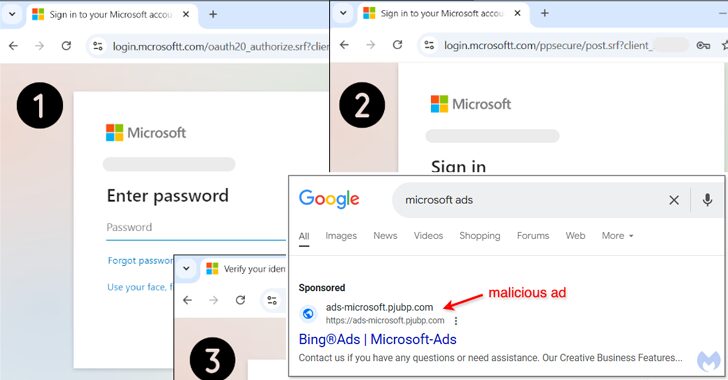
Malvertising Scam Uses Fake Google Ads to Hijack Microsoft Advertising Accounts
[ad_1] Feb 01, 2025Ravie LakshmananMalvertising / Mobile Security Cybersecurity researchers have discovered a malvertising campaign that’s targeting Microsoft advertisers with bogus Google ads that aim to take them to phishing pages that are capable of harvesting their credentials. “These malicious ads, appearing on Google Search, are designed to steal the login information of users trying…
CISA and FDA Warn of Critical Backdoor in Contec CMS8000 Patient Monitors
[ad_1] Jan 31, 2025Ravie LakshmananVulnerability / Healthcare The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Food and Drug Administration (FDA) have issued alerts about the presence of hidden functionality in Contec CMS8000 patient monitors and Epsimed MN-120 patient monitors. The vulnerability, tracked as CVE-2025-0626, carries a CVSS v4 score of 7.7 on a…
Google Bans 158,000 Malicious Android App Developer Accounts in 2024
[ad_1] Google said it blocked over 2.36 million policy-violating Android apps from being published to the Google Play app marketplace in 2024 and banned more than 158,000 bad developer accounts that attempted to publish such harmful apps. The tech giant also noted it prevented 1.3 million apps from getting excessive or unnecessary access to sensitive…
Italy Bans Chinese DeepSeek AI Over Data Privacy and Ethical Concerns
[ad_1] Italy’s data protection watchdog has blocked Chinese artificial intelligence (AI) firm DeepSeek’s service within the country, citing a lack of information on its use of users’ personal data. The development comes days after the authority, the Garante, sent a series of questions to DeepSeek, asking about its data handling practices and where it obtained…
Top 5 AI-Powered Social Engineering Attacks
[ad_1] Social engineering has long been an effective tactic because of how it focuses on human vulnerabilities. There’s no brute-force ‘spray and pray’ password guessing. No scouring systems for unpatched software. Instead, it simply relies on manipulating emotions such as trust, fear, and respect for authority, usually with the goal of gaining access to sensitive…
Broadcom Patches VMware Aria Flaws – Exploits May Lead to Credential Theft
[ad_1] Jan 31, 2025Ravie LakshmananVulnerability / Data Security Broadcom has released security updates to patch five security flaws impacting VMware Aria Operations and Aria Operations for Logs, warning customers that attackers could exploit them to gain elevated access or obtain sensitive information. The list of identified flaws, which impact versions 8.x of the software, is…
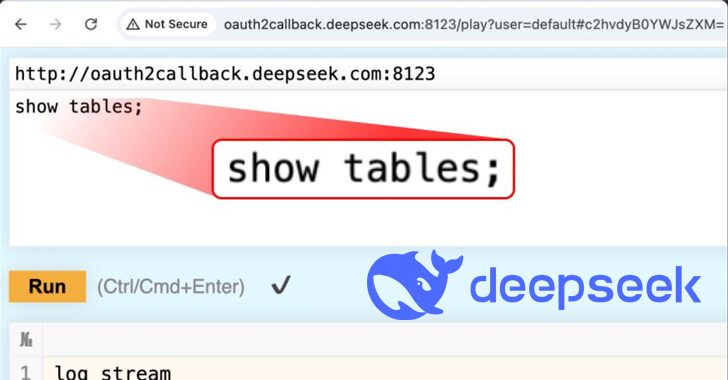
Over 1 Million Log Lines, Secret Keys Leaked
[ad_1] Jan 30, 2025Ravie LakshmananArtificial Intelligence / Data Privacy Buzzy Chinese artificial intelligence (AI) startup DeepSeek, which has had a meteoric rise in popularity in recent days, left one of its databases exposed on the internet, which could have allowed malicious actors to gain access to sensitive data. The ClickHouse database “allows full control over…