[ad_1] Jan 28, 2025Ravie LakshmananArtificial Intelligence / Technology DeepSeek, the Chinese AI startup that has captured much of the artificial intelligence (AI) buzz in recent days, said it’s restricting registrations on the service, citing malicious attacks. “Due to large-scale malicious attacks on DeepSeek’s services, we are temporarily limiting registrations to ensure continued service,” the company…
Category: Cyber News
Apple Patches Actively Exploited Zero-Day Affecting iPhones, Macs, and More
[ad_1] Jan 28, 2025Ravie LakshmananVulnerability / Endpoint Security Apple has released software updates to address several security flaws across its portfolio, including a zero-day vulnerability that it said has been exploited in the wild. The vulnerability, tracked as CVE-2025-24085, has been described as a use-after-free bug in the Core Media component that could permit a…
GitHub Desktop Vulnerability Risks Credential Leaks via Malicious Remote URLs
[ad_1] Jan 27, 2025Ravie LakshmananVulnerability / Software Security Multiple security vulnerabilities have been disclosed in GitHub Desktop as well as other Git-related projects that, if successfully exploited, could permit an attacker to gain unauthorized access to a user’s Git credentials. “Git implements a protocol called Git Credential Protocol to retrieve credentials from the credential helper,”…
Top Cybersecurity Threats, Tools and Tips [27 January]
[ad_1] Jan 27, 2025Ravie LakshmananCybersecurity / Recap Welcome to your weekly cybersecurity scoop! Ever thought about how the same AI meant to protect our hospitals could also compromise them? This week, we’re breaking down the sophisticated world of AI-driven threats, key updates in regulations, and some urgent vulnerabilities in healthcare tech that need our attention….
Do We Really Need The OWASP NHI Top 10?
[ad_1] The Open Web Application Security Project has recently introduced a new Top 10 project – the Non-Human Identity (NHI) Top 10. For years, OWASP has provided security professionals and developers with essential guidance and actionable frameworks through its Top 10 projects, including the widely used API and Web Application security lists. Non-human identity security…
GamaCopy Mimics Gamaredon Tactics in Cyber Espionage Targeting Russian Entities
[ad_1] Jan 27, 2025Ravie LakshmananCyber Espionage / Threat Intelligence A previously unknown threat actor has been observed copying the tradecraft associated with the Kremlin-aligned Gamaredon hacking group in its cyber attacks targeting Russian-speaking entities. The campaign has been attributed to a threat cluster dubbed GamaCopy, which is assessed to share overlaps with another hacking group…
MintsLoader Delivers StealC Malware and BOINC in Targeted Cyber Attacks
[ad_1] Jan 27, 2025Ravie LakshmananMalware / SEO Poisoning Threat hunters have detailed an ongoing campaign that leverages a malware loader called MintsLoader to distribute secondary payloads such as the StealC information stealer and a legitimate open-source network computing platform called BOINC. “MintsLoader is a PowerShell based malware loader that has been seen delivered via spam…
Meta’s Llama Framework Flaw Exposes AI Systems to Remote Code Execution Risks
[ad_1] A high-severity security flaw has been disclosed in Meta’s Llama large language model (LLM) framework that, if successfully exploited, could allow an attacker to execute arbitrary code on the llama-stack inference server. The vulnerability, tracked as CVE-2024-50050, has been assigned a CVSS score of 6.3 out of 10.0. Supply chain security firm Snyk, on…
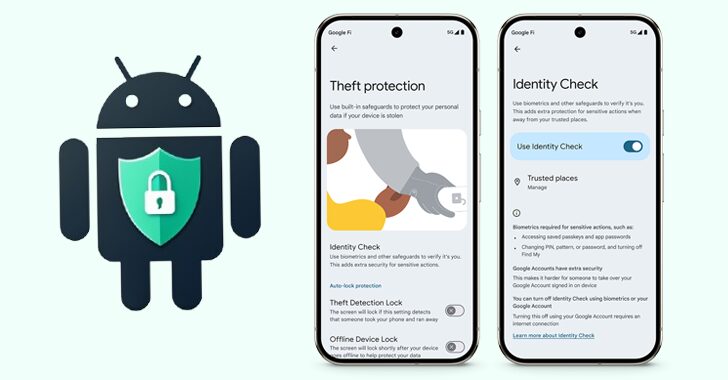
Android’s New Identity Check Feature Locks Device Settings Outside Trusted Locations
[ad_1] Jan 24, 2025Ravie LakshmananBiometric / Mobile Security Google has launched a new feature called Identity Check for supported Android devices that locks sensitive settings behind biometric authentication when outside of trusted locations. “When you turn on Identity Check, your device will require explicit biometric authentication to access certain sensitive resources when you’re outside of…
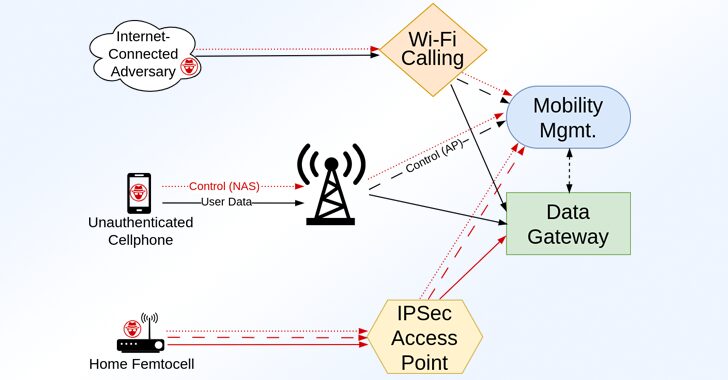
Over 100 Security Flaws Found in LTE and 5G Network Implementations
[ad_1] Jan 24, 2025Ravie LakshmananTelecom Security / Vulnerability A group of academics has disclosed details of over 100 security vulnerabilities impacting LTE and 5G implementations that could be exploited by an attacker to disrupt access to service and even gain a foothold into the cellular core network. The 119 vulnerabilities, assigned 97 unique CVE identifiers,…