[ad_1] The modern workplace has undergone a seismic transformation over recent years, with hybrid work becoming the norm and businesses rapidly adopting cloud-based Software-as-a-Service (SaaS) applications to facilitate it. SaaS applications like Microsoft 365 and Google Workspace have now become the backbone of business operations, enabling seamless collaboration and productivity. However, this dependence on SaaS…
Category: Cyber News
DoJ Indicts 5 Individuals for $866K North Korean IT Worker Scheme Violations
[ad_1] The U.S. Department of Justice (DoJ) on Thursday indicted two North Korean nationals, a Mexican national, and two of its own citizens for their alleged involvement in the ongoing fraudulent information technology (IT) worker scheme that seeks to generate revenue for the Democratic People’s Republic of Korea (DPRK) in violation of international sanctions. The…
How Satori Secures Sensitive Data From Production to AI
[ad_1] Every week seems to bring news of another data breach, and it’s no surprise why: securing sensitive data has become harder than ever. And it’s not just because companies are dealing with orders of magnitude more data. Data flows and user roles are constantly shifting, and data is stored across multiple technologies and cloud…
CISA Adds Five-Year-Old jQuery XSS Flaw to Exploited Vulnerabilities List
[ad_1] Jan 24, 2025Ravie LakshmananVulnerability / JavaScript The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday placed a now-patched security flaw impacting the popular jQuery JavaScript library to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The medium-severity vulnerability is CVE-2020-11023 (CVSS score: 6.1/6.9), a nearly five-year-old cross-site scripting (XSS)…
Top Cybersecurity Threats, Tools and Tips [20 January]
[ad_1] Jan 20, 2025Ravie Lakshmanan As the digital world becomes more complicated, the lines between national security and cybersecurity are starting to fade. Recent cyber sanctions and intelligence moves show a reality where malware and fake news are used as tools in global politics. Every cyberattack now seems to have deeper political consequences. Governments are…
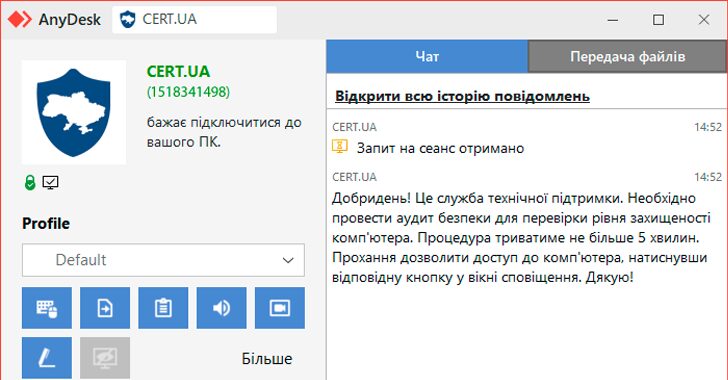
CERT-UA Warns of Cyber Scams Using Fake AnyDesk Requests for Fraudulent Security Audits
[ad_1] Jan 21, 2025Ravie LakshmananMalware / Cyber Threat The Computer Emergency Response Team of Ukraine (CERT-UA) is warning of ongoing attempts by unknown threat actors to impersonate the cybersecurity agency by sending AnyDesk connection requests. The AnyDesk requests claim to be for conducting an audit to assess the “level of security,” CERT-UA added, cautioning organizations…
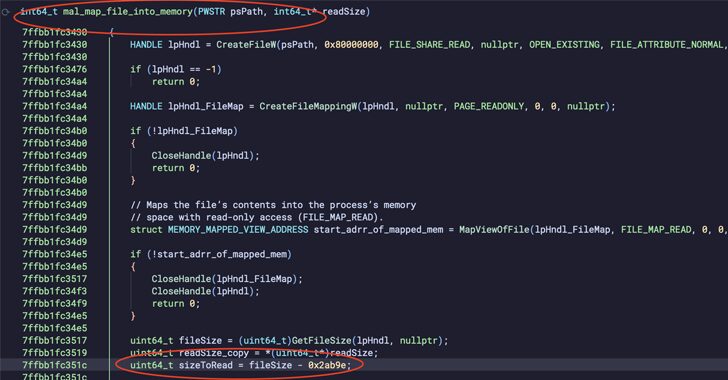
PNGPlug Loader Delivers ValleyRAT Malware Through Fake Software Installers
[ad_1] Jan 21, 2025Ravie LakshmananCyber Attack / Windows Security Cybersecurity researchers are calling attention to a series of cyber attacks that have targeted Chinese-speaking regions like Hong Kong, Taiwan, and Mainland China with a known malware called ValleyRAT. The attacks leverage a multi-stage loader dubbed PNGPlug to deliver the ValleyRAT payload, Intezer said in a…
Ex-CIA Analyst Pleads Guilty to Sharing Top-Secret Data with Unauthorized Parties
[ad_1] A former analyst working for the U.S. Central Intelligence Agency (CIA) pleaded guilty to transmitting top secret National Defense Information (NDI) to individuals who did not have the necessary authorization to receive it and attempted to cover up the activity. Asif William Rahman, 34, of Vienna, was an employee of the CIA since 2016…
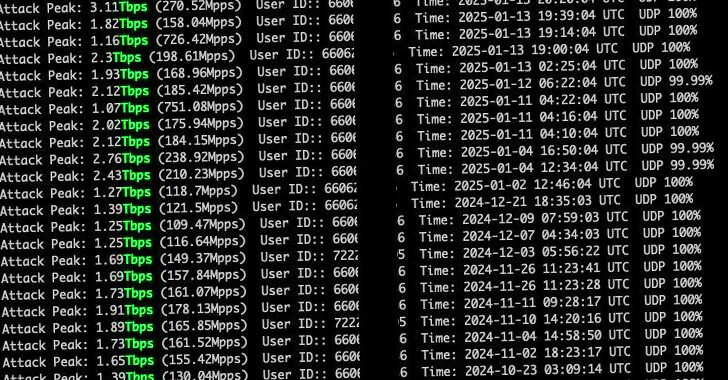
Mirai Botnet Launches Record 5.6 Tbps DDoS Attack with 13,000+ IoT Devices
[ad_1] Jan 22, 2025Ravie LakshmananBotnet / Network Security Web infrastructure and security company Cloudflare on Tuesday said it detected and blocked a 5.6 Terabit per second (Tbps) distributed denial-of-service (DDoS) attack, the largest ever attack to be reported to date. The UDP protocol-based attack took place on October 29, 2024, targeting one of its customers,…
Oracle Releases January 2025 Patch to Address 318 Flaws Across Major Products
[ad_1] Jan 22, 2025Ravie LakshmananVulnerability / Enterprise Security Oracle is urging customers to apply its January 2025 Critical Patch Update (CPU) to address 318 new security vulnerabilities spanning its products and services. The most severe of the flaws is a bug in the Oracle Agile Product Lifecycle Management (PLM) Framework (CVE-2025-21556, CVSS score: 9.9) that…