[ad_1] Jan 23, 2025Ravie LakshmananMalware / Enterprise Security Enterprise-grade Juniper Networks routers have become the target of a custom backdoor as part of a campaign dubbed J-magic. According to the Black Lotus Labs team at Lumen Technologies, the activity is so named for the fact that the backdoor continuously monitors for a “magic packet” sent…
Category: Cyber News
The State of Web Exposure 2025
[ad_1] Are your websites leaking sensitive data? New research reveals that 45% of third-party apps access user info without proper authorization, and 53% of risk exposures in Retail are due to the excessive use of tracking tools. Learn how to uncover and mitigate these hidden threats and risks—download the full report here. New research by…
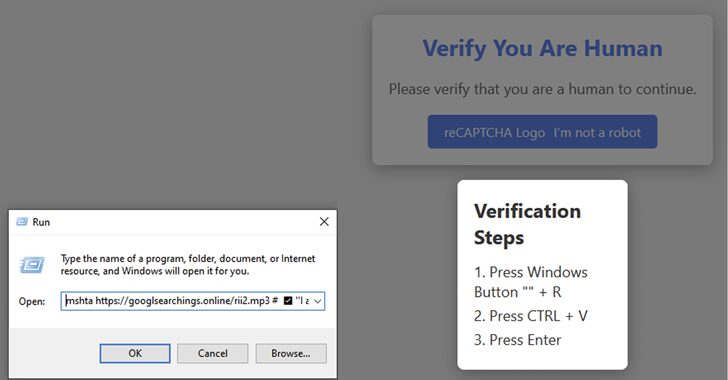
Fake CAPTCHA Campaign Spreads Lumma Stealer in Multi-Industry Attacks
[ad_1] Jan 23, 2025Ravie LakshmananPhishing / Malware Cybersecurity researchers are calling attention to a new malware campaign that leverages fake CAPTCHA verification checks to deliver the infamous Lumma information stealer. “The campaign is global, with Netskope Threat Labs tracking victims targeted in Argentina, Colombia, the United States, the Philippines, and other countries around the world,”…
Palo Alto Firewalls Found Vulnerable to Secure Boot Bypass and Firmware Exploits
[ad_1] Jan 23, 2025Ravie LakshmananFirmware Security / Vulnerability An exhaustive evaluation of three firewall models from Palo Alto Networks has uncovered a host of known security flaws impacting the devices’ firmware as well as misconfigured security features. “These weren’t obscure, corner-case vulnerabilities,” security vendor Eclypsium said in a report shared with The Hacker News. “Instead…
Experts Find Shared Codebase Linking Morpheus and HellCat Ransomware Payloads
[ad_1] Jan 23, 2025Ravie LakshmananThreat Intelligence / Data Breach An analysis of HellCat and Morpheus ransomware operations has revealed that affiliates associated with the respective cybercrime entities are using identical code for their ransomware payloads. The findings come from SentinelOne, which analyzed artifacts uploaded to the VirusTotal malware scanning platform by the same submitter towards…
SonicWall Urges Immediate Patch for Critical CVE-2025-23006 Flaw Amid Likely Exploitation
[ad_1] Jan 23, 2025Ravie LakshmananVulnerability / Network Security SonicWall is alerting customers of a critical security flaw impacting its Secure Mobile Access (SMA) 1000 Series appliances that it said has been likely exploited in the wild as a zero-day. The vulnerability, tracked as CVE-2025-23006, is rated 9.8 out of a maximum of 10.0 on the…
How to Eliminate Identity-Based Threats
[ad_1] Despite significant investments in advanced technologies and employee training programs, credential and user-based attacks remain alarmingly prevalent, accounting for 50-80% of enterprise breaches[1],[2]. While identity-based attacks continue to dominate as the leading cause of security incidents, the common approach to identity security threats is still threat reduction, implementing layers of controls to reduce risk…
QakBot-Linked BC Malware Adds Enhanced Remote Access and Data Gathering Features
[ad_1] Jan 23, 2025Ravie LakshmananMalware / Threat Intelligence Cybersecurity researchers have disclosed details of a new BackConnect (BC) malware that has been developed by threat actors linked to the infamous QakBot loader. “BackConnect is a common feature or module utilized by threat actors to maintain persistence and perform tasks,” Walmart’s Cyber Intelligence team told The…
Cisco Fixes Critical Privilege Escalation Flaw in Meeting Management (CVSS 9.9)
[ad_1] Jan 23, 2025Ravie LakshmananNetwork Security / Vulnerability Cisco has released software updates to address a critical security flaw impacting Meeting Management that could permit a remote, authenticated attacker to gain administrator privileges on susceptible instances. The vulnerability, tracked as CVE-2025-20156, carries a CVSS score of 9.9 out 10.0. It has been described as a…
TRIPLESTRENGTH Hits Cloud for Cryptojacking, On-Premises Systems for Ransomware
[ad_1] Jan 23, 2025Ravie LakshmananCloud Security / Cryptojacking Google on Wednesday shed light on a financially motivated threat actor named TRIPLESTRENGTH for its opportunistic targeting of cloud environments for cryptojacking and on-premise ransomware attacks. “This actor engaged in a variety of threat activity, including cryptocurrency mining operations on hijacked cloud resources and ransomware activity,” the…