[ad_1] Why does ICS/OT need specific controls and its own cybersecurity budget today? Because treating ICS/OT security with an IT security playbook isn’t just ineffective—it’s high risk. In the rapidly evolving domain of cybersecurity, the specific challenges and needs for Industrial Control Systems (ICS) and Operational Technology (OT) security distinctly stand out from traditional IT…
Category: Cyber News
Google Cloud Researchers Uncover Flaws in Rsync File Synchronization Tool
[ad_1] Jan 15, 2025Ravie LakshmananVulnerability / Software Update As many as six security vulnerabilities have been disclosed in the popular Rsync file-synchronizing tool for Unix systems, some of which could be exploited to execute arbitrary code on a client. “Attackers can take control of a malicious server and read/write arbitrary files of any connected client,”…
Lazarus Group Targets Web3 Developers with Fake LinkedIn Profiles in Operation 99
[ad_1] Jan 15, 2025Ravie LakshmananCryptocurrency / Malware The North Korea-linked Lazarus Group has been attributed to a new cyber attack campaign dubbed Operation 99 that targeted software developers looking for freelance Web3 and cryptocurrency work to deliver malware. “The campaign begins with fake recruiters, posing on platforms like LinkedIn, luring developers with project tests and…
Researcher Uncovers Critical Flaws in Multiple Versions of Ivanti Endpoint Manager
[ad_1] Jan 16, 2025Ravie LakshmananVulnerability / Endpoint Security Ivanti has rolled out security updates to address several security flaws impacting Avalanche, Application Control Engine, and Endpoint Manager (EPM), including four critical bugs that could lead to information disclosure. All the four critical security flaws, rated 9.8 out of 10.0 on the CVSS scale, are rooted…
Hackers Hide Malware in Images to Deploy VIP Keylogger and 0bj3ctivity Stealer
[ad_1] Jan 16, 2025Ravie LakshmananMalware / Ransomware Threat actors have been observed concealing malicious code in images to deliver malware such as VIP Keylogger and 0bj3ctivity Stealer as part of separate campaigns. “In both campaigns, attackers hid malicious code in images they uploaded to archive[.]org, a file-hosting website, and used the same .NET loader to…
Researchers Find Exploit Allowing NTLMv1 Despite Active Directory Restrictions
[ad_1] Jan 16, 2025Ravie LakshmananActive Directory / Vulnerability Cybersecurity researchers have found that the Microsoft Active Directory Group Policy that’s designed to disable NT LAN Manager (NTLM) v1 can be trivially bypassed by a misconfiguration. “A simple misconfiguration in on-premise applications can override the Group Policy, effectively negating the Group Policy designed to stop NTLMv1…
Russian Star Blizzard Shifts Tactics to Exploit WhatsApp QR Codes for Credential Harvesting
[ad_1] Jan 16, 2025Ravie LakshmananSpear Phishing / Threat Intelligence The Russian threat actor known as Star Blizzard has been linked to a new spear-phishing campaign that targets victims’ WhatsApp accounts, signaling a departure from its longstanding tradecraft in a likely attempt to evade detection. “Star Blizzard’s targets are most commonly related to government or diplomacy…
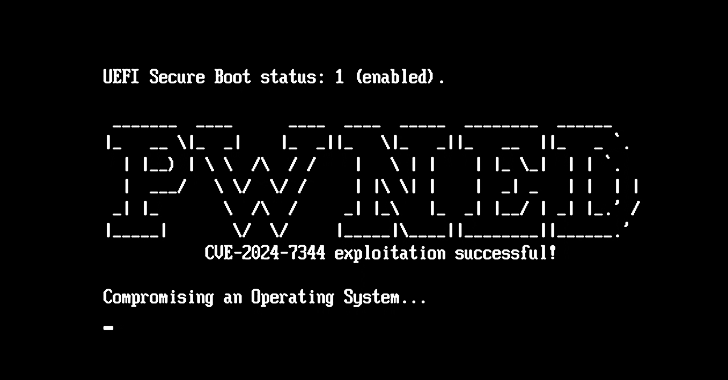
New UEFI Secure Boot Vulnerability Could Allow Attackers to Load Malicious Bootkits
[ad_1] Jan 16, 2025Ravie LakshmananVulnerability / Cybersecurity Details have emerged about a now-patched security vulnerability that could allow a bypass of the Secure Boot mechanism in Unified Extensible Firmware Interface (UEFI) systems. The vulnerability, assigned the CVE identifier CVE-2024-7344 (CVSS score: 6.7), resides in a UEFI application signed by Microsoft’s “Microsoft Corporation UEFI CA 2011”…
The $10 Cyber Threat Responsible for the Biggest Breaches of 2024
[ad_1] You can tell the story of the current state of stolen credential-based attacks in three numbers: Stolen credentials were the #1 attacker action in 2023/24, and the breach vector for 80% of web app attacks. (Source: Verizon). Cybersecurity budgets grew again in 2024, with organizations now spending almost $1,100 per user (Source: Forrester). Stolen…
Ready to Simplify Trust Management? Join Free Webinar to See DigiCert ONE in Action
[ad_1] Jan 16, 2025The Hacker NewsCertificate Management / Compliance The digital world is exploding. IoT devices are multiplying like rabbits, certificates are piling up faster than you can count, and compliance requirements are tightening by the day. Keeping up with it all can feel like trying to juggle chainsaws while riding a unicycle. Traditional trust…