[ad_1] Dec 24, 2024Ravie LakshmananVulnerability / Zero Day The Apache Software Foundation (ASF) has released a security update to address an important vulnerability in its Tomcat server software that could result in remote code execution (RCE) under certain conditions. The vulnerability, tracked as CVE-2024-56337, has been described as an incomplete mitigation for CVE-2024-50379 (CVSS score:…
Category: Cyber News
Critical SQL Injection Vulnerability in Apache Traffic Control Rated 9.9 CVSS — Patch Now
[ad_1] Dec 25, 2024Ravie LakshmananServer Security / Vulnerability The Apache Software Foundation (ASF) has shipped security updates to address a critical security flaw in Traffic Control that, if successfully exploited, could allow an attacker to execute arbitrary Structured Query Language (SQL) commands in the database. The SQL injection vulnerability, tracked as CVE-2024-45387, is rated 9.9…
Ruijie Networks’ Cloud Platform Flaws Could Expose 50,000 Devices to Remote Attacks
[ad_1] Dec 25, 2024Ravie LakshmananCloud Security / Vulnerability Cybersecurity researchers have discovered several security flaws in the cloud management platform developed by Ruijie Networks that could permit an attacker to take control of the network appliances. “These vulnerabilities affect both the Reyee platform, as well as Reyee OS network devices,” Claroty researchers Noam Moshe and…
A New C++ Variant of BellaCiao Malware
[ad_1] Dec 25, 2024Ravie LakshmananCyber Attack / Malware The Iranian nation-state hacking group known as Charming Kitten has been observed deploying a C++ variant of a known malware called BellaCiao. Russian cybersecurity company Kaspersky, which dubbed the new version BellaCPP, said it discovered the artifact as part of a “recent” investigation into a compromised machine…
CISA Adds Acclaim USAHERDS Vulnerability to KEV Catalog Amid Active Exploitation
[ad_1] Dec 24, 2024Ravie LakshmananVulnerability / Software Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a now-patched high-severity security flaw impacting Acclaim Systems USAHERDS to the Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation in the wild. The vulnerability in question is CVE-2021-44207 (CVSS score: 8.1), a case…
Researchers Uncover PyPI Packages Stealing Keystrokes and Hijacking Social Accounts
[ad_1] Dec 24, 2024Ravie LakshmananMalware / Data Exfiltration Cybersecurity researchers have flagged two malicious packages that were uploaded to the Python Package Index (PyPI) repository and came fitted with capabilities to exfiltrate sensitive information from compromised hosts, according to new findings from Fortinet FortiGuard Labs. The packages, named zebo and cometlogger, attracted 118 and 164…
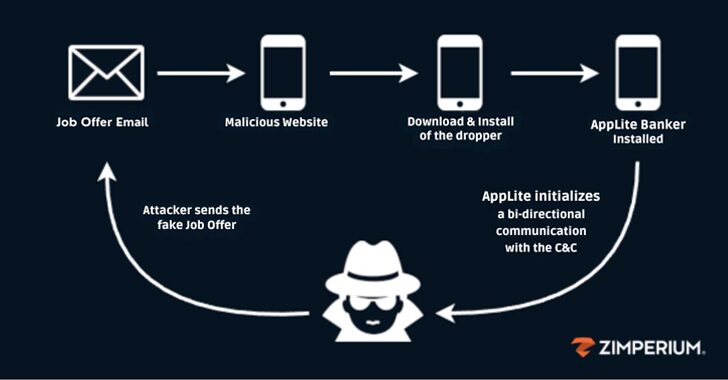
North Korean Hackers Pull Off $308M Bitcoin Heist from Crypto Firm DMM Bitcoin
[ad_1] Dec 24, 2024Ravie LakshmananCybercrime / Malware Japanese and U.S. authorities have formerly attributed the theft of cryptocurrency worth $308 million from cryptocurrency company DMM Bitcoin in May 2024 to North Korean cyber actors. “The theft is affiliated with TraderTraitor threat activity, which is also tracked as Jade Sleet, UNC4899, and Slow Pisces,” the agencies…
Top Cybersecurity Threats, Tools and Tips
[ad_1] Dec 23, 2024Ravie LakshmananCybersecurity / Weekly Recap The online world never takes a break, and this week shows why. From ransomware creators being caught to hackers backed by governments trying new tricks, the message is clear: cybercriminals are always changing how they attack, and we need to keep up. Hackers are using everyday tools…
AI Could Generate 10,000 Malware Variants, Evading Detection in 88% of Case
[ad_1] Dec 23, 2024Ravie LakshmananMachine Learning / Threat Analysis Cybersecurity researchers have found that it’s possible to use large language models (LLMs) to generate new variants of malicious JavaScript code at scale in a manner that can better evade detection. “Although LLMs struggle to create malware from scratch, criminals can easily use them to rewrite…
Rockstar2FA Collapse Fuels Expansion of FlowerStorm Phishing-as-a-Service
[ad_1] Dec 23, 2024Ravie LakshmananPhishing / Cybercrime An interruption to the phishing-as-a-service (PhaaS) toolkit called Rockstar 2FA has led to a rapid uptick in activity from another nascent offering named FlowerStorm. “It appears that the [Rockstar2FA] group running the service experienced at least a partial collapse of its infrastructure, with pages associated with the service…