[ad_1] Dec 11, 2024Ravie LakshmananCyber Espionage / Cyber Attack A suspected China-based threat actor has been linked to a series of cyber attacks targeting high-profile organizations in Southeast Asia since at least October 2023. The espionage campaign targeted organizations in various sectors spanning government ministries in two different countries, an air traffic control organization, a…
Category: Cyber News
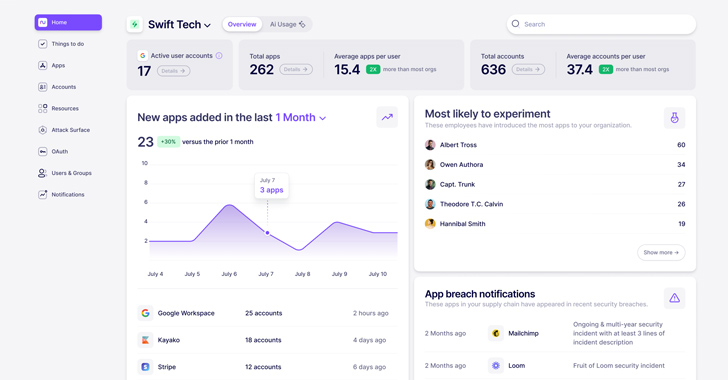
What is Nudge Security and How Does it Work?
[ad_1] Dec 11, 2024The Hacker NewsSaaS Security / Endpoint Security Regain control of SaaS sprawl with Day One discovery of all SaaS and GenAI accounts along with workflows to help you mitigate security risks, curb rogue app usage, and manage SaaS spend. In today’s highly distributed workplace, every employee has the ability to act as…
Germany Disrupts BADBOX Malware on 30,000 Devices Using Sinkhole Action
[ad_1] Dec 14, 2024Ravie LakshmananBotnet / Ad Fraud Germany’s Federal Office of Information Security (BSI) has announced that it has disrupted a malware operation called BADBOX that came preloaded on at least 30,000 internet-connected devices sold across the country. In a statement published earlier this week, authorities said they severed the communications between the devices…
Thai Officials Targeted in Yokai Backdoor Campaign Using DLL Side-Loading Techniques
[ad_1] Dec 14, 2024Ravie LakshmananMalware / Cyber Threat Thai government officials have emerged as the target of a new campaign that leverages a technique called DLL side-loading to deliver a previously undocumented backdoor dubbed Yokai. “The target of the threat actors were Thailand officials based on the nature of the lures,” Nikhil Hegde, senior engineer…
Chinese EagleMsgSpy Spyware Found Exploiting Mobile Devices Since 2017
[ad_1] Cybersecurity researchers have discovered a novel surveillance program that’s suspected to be used by Chinese police departments as a lawful intercept tool to gather a wide range of information from mobile devices. The Android tool, codenamed EagleMsgSpy by Lookout, has been operational since at least 2017, with artifacts uploaded to the VirusTotal malware scanning…
ZLoader Malware Returns With DNS Tunneling to Stealthily Mask C2 Comms
[ad_1] Dec 11, 2024Ravie LakshmananRansomware / Malware Cybersecurity researchers have discovered a new version of the ZLoader malware that employs a Domain Name System (DNS) tunnel for command-and-control (C2) communications, indicating that the threat actors are continuing to refine the tool after resurfacing a year ago. “Zloader 2.9.4.0 adds notable improvements including a custom DNS…
Microsoft MFA AuthQuake Flaw Enabled Unlimited Brute-Force Attempts Without Alerts
[ad_1] Dec 11, 2024Ravie LakshmananVulnerability / Authentication Cybersecurity researchers have flagged a “critical” security vulnerability in Microsoft’s multi-factor authentication (MFA) implementation that allows an attacker to trivially sidestep the protection and gain unauthorized access to a victim’s account. “The bypass was simple: it took around an hour to execute, required no user interaction and did…
WordPress Hunk Companion Plugin Flaw Exploited to Silently Install Vulnerable Plugins
[ad_1] Dec 12, 2024Ravie LakshmananWebsite Security / Vulnerability Malicious actors are exploiting a critical vulnerability in the Hunk Companion plugin for WordPress to install other vulnerable plugins that could open the door to a variety of attacks. The flaw, tracked as CVE-2024-11972 (CVSS score: 9.8), affects all versions of the plugin prior to 1.9.0. The…
SaaS Budget Planning Guide for IT Professionals
[ad_1] SaaS services are one of the biggest drivers of OpEx (operating expenses) for modern businesses. With Gartner projecting $247.2 billion in global SaaS spending this year, it’s no wonder SaaS budgets are a big deal in the world of finance and IT. Efficient SaaS utilization can significantly affect both the bottom line and employee…
Researchers Uncover Symlink Exploit Allowing TCC Bypass in iOS and macOS
[ad_1] Dec 12, 2024Ravie LakshmananVulnerability / Device Security Details have emerged about a now-patched security vulnerability in Apple’s iOS and macOS that, if successfully exploited, could sidestep the Transparency, Consent, and Control (TCC) framework and result in unauthorized access to sensitive information. The flaw, tracked as CVE-2024-44131 (CVSS score: 5.3), resides in the FileProvider component,…