[ad_1] Multi-stage cyber attacks, characterized by their complex execution chains, are designed to avoid detection and trick victims into a false sense of security. Knowing how they operate is the first step to building a solid defense strategy against them. Let’s examine real-world examples of some of the most common multi-stage attack scenarios that are…
Category: Cyber News
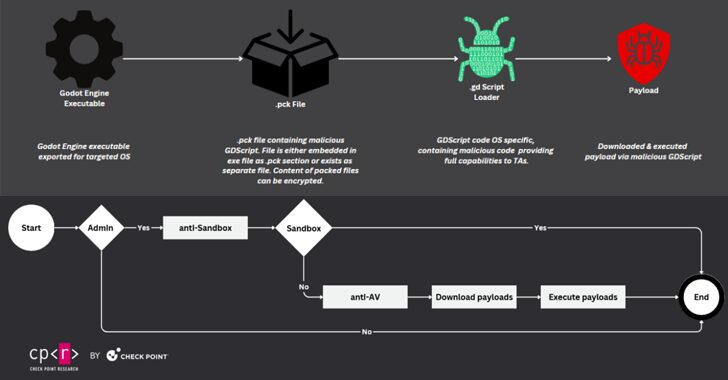
Cybercriminals Exploit Popular Game Engine Godot to Distribute Cross-Platform Malware
[ad_1] A popular open-source game engine called Godot Engine is being misused as part of a new GodLoader malware campaign, infecting over 17,000 systems since at least June 2024. “Cybercriminals have been taking advantage of Godot Engine to execute crafted GDScript code which triggers malicious commands and delivers malware,” Check Point said in a new…
XML-RPC npm Library Turns Malicious, Steals Data, Deploys Crypto Miner
[ad_1] Nov 28, 2024Ravie LakshmananSoftware Security / Data Breach Cybersecurity researchers have discovered a software supply chain attack that has remained active for over a year on the npm package registry by starting off as an innocuous library and later adding malicious code to steal sensitive data and mine cryptocurrency on infected systems. The package,…
Microsoft Fixes AI, Cloud, and ERP Security Flaws; One Exploited in Active Attacks
[ad_1] Nov 29, 2024Ravie LakshmananAI Security / Cloud Security Microsoft has addressed four security flaws impacting its artificial intelligence (AI), cloud, enterprise resource planning, and Partner Center offerings, including one that it said has been exploited in the wild. The vulnerability that has been tagged with an “Exploitation Detected” assessment is CVE-2024-49035 (CVSS score: 8.7),…
Wanted Russian Hacker Linked to Hive and LockBit Ransomware Arrested
[ad_1] Nov 30, 2024Mohit KumarRansomware / Cybercrime A Russian cybercriminal wanted in the U.S. in connection with LockBit and Hive ransomware operations has been arrested by law enforcement authorities in the country. According to a news report from Russian media outlet RIA Novosti, Mikhail Pavlovich Matveev has been accused of developing a malicious program designed…
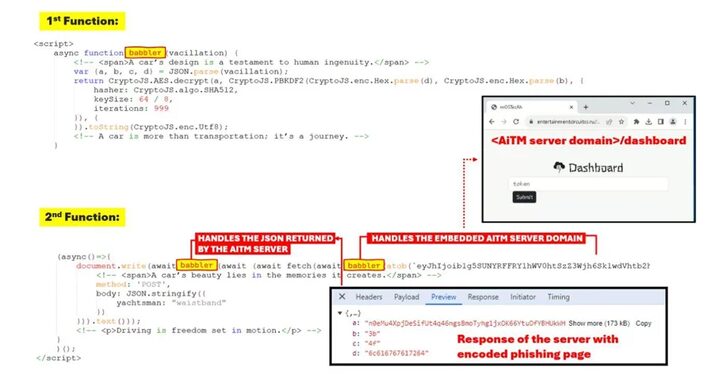
Phishing-as-a-Service “Rockstar 2FA” Targets Microsoft 365 Users with AiTM Attacks
[ad_1] Nov 29, 2024Ravie LakshmananCybercrime / Cloud Security Cybersecurity researchers are warning about malicious email campaigns leveraging a phishing-as-a-service (PhaaS) toolkit called Rockstar 2FA with an aim to steal Microsoft 365 account credentials. “This campaign employs an AitM [adversary-in-the-middle] attack, allowing attackers to intercept user credentials and session cookies, which means that even users with…
Protecting Tomorrow’s World: Shaping the Cyber-Physical Future
[ad_1] The lines between digital and physical realms increasingly blur. While this opens countless opportunities for businesses, it also brings numerous challenges. In our recent webinar, Shaping the Cyber-Physical Future: Trends, Challenges, and Opportunities for 2025, we explored the different factors shaping the cyber-physical future. In an insightful conversation with industry experts, we discussed the…
AI-Powered Fake News Campaign Targets Western Support for Ukraine and U.S. Elections
[ad_1] Nov 29, 2024Ravie LakshmananDisinformation / Artificial Intelligence A Moscow-based company sanctioned by the U.S. earlier this year has been linked to yet another influence operation designed to turn public opinion against Ukraine and erode Western support since at least December 2023. The covert campaign undertaken by Social Design Agency (SDA), leverages videos enhanced using…
U.S. Citizen Sentenced for Spying on Behalf of China’s Intelligence Agency
[ad_1] Nov 29, 2024Ravie LakshmananCorporate Espionage / National Security A 59-year-old U.S. citizen who immigrated from the People’s Republic of China (PRC) has been sentenced to four years in prison for conspiring to act as a spy for the country and sharing sensitive information about his employer with China’s principal civilian intelligence agency. Ping Li,…
Over Two Dozen Flaws Identified in Advantech Industrial Wi-Fi Access Points – Patch ASAP
[ad_1] Nov 28, 2024Ravie LakshmananIoT Security / Vulnerability Nearly two dozen security vulnerabilities have been disclosed in Advantech EKI industrial-grade wireless access point devices, some of which could be weaponized to bypass authentication and execute code with elevated privileges. “These vulnerabilities pose significant risks, allowing unauthenticated remote code execution with root privileges, thereby fully compromising…