[ad_1] Nov 12, 2024Ravie LakshmananEmail Security / Threat Intelligence Cybersecurity researchers are calling attention to a new sophisticated tool called GoIssue that can be used to send phishing messages at scale targeting GitHub users. The program, first marketed by a threat actor named cyberdluffy (aka Cyber D’ Luffy) on the Runion forum earlier this August,…
Category: Cyber News
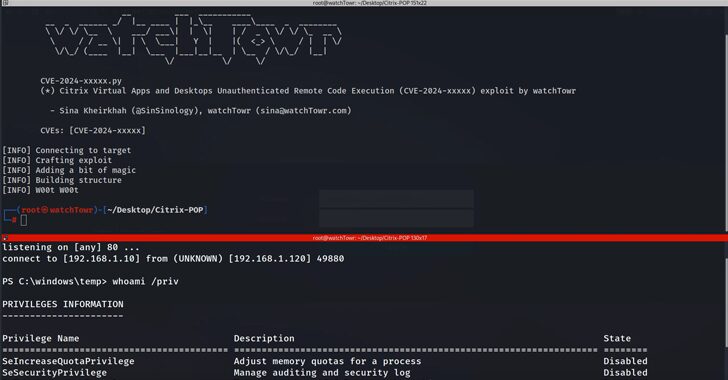
New Flaws in Citrix Virtual Apps Enable RCE Attacks via MSMQ Misconfiguration
[ad_1] Nov 12, 2024Ravie LakshmananVirtualization / Vulnerability Cybersecurity researchers have disclosed new security flaws impacting Citrix Virtual Apps and Desktop that could be exploited to achieve unauthenticated remote code execution (RCE) The issue, per findings from watchTowr, is rooted in the Session Recording component that allows system administrators to capture user activity, and record keyboard…
New Ymir Ransomware Exploits Memory for Stealthy Attacks; Targets Corporate Networks
[ad_1] Cybersecurity researchers have flagged a new ransomware family called Ymir that was deployed in an attack two days after systems were compromised by a stealer malware called RustyStealer. “Ymir ransomware introduces a unique combination of technical features and tactics that enhance its effectiveness,” Russian cybersecurity vendor Kaspersky said. “Threat actors leveraged an unconventional blend…
New GootLoader Campaign Targets Users Searching for Bengal Cat Laws in Australia
[ad_1] Nov 11, 2024Ravie LakshmananMalware / SEO Poisoning In an unusually specific campaign, users searching about the legality of Bengal Cats in Australia are being targeted with the GootLoader malware. “In this case, we found the GootLoader actors using search results for information about a particular cat and a particular geography being used to deliver…
THN Recap: Top Cybersecurity Threats, Tools, and Practices (Nov 04
[ad_1] Nov 11, 2024Ravie LakshmananCybersecurity / Hacking News ⚠️ Imagine this: the very tools you trust to protect you online—your two-factor authentication, your car’s tech system, even your security software—turned into silent allies for hackers. Sounds like a scene from a thriller, right? Yet, in 2024, this isn’t fiction; it’s the new cyber reality. Today’s…
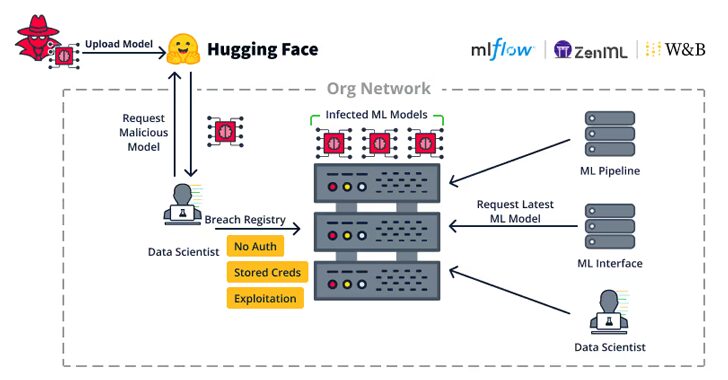
Security Flaws in Popular ML Toolkits Enable Server Hijacks, Privilege Escalation
[ad_1] Nov 11, 2024Ravie LakshmananMachine Learning / Vulnerability Cybersecurity researchers have uncovered nearly two dozen security flaws spanning 15 different machine learning (ML) related open-source projects. These comprise vulnerabilities discovered both on the server- and client-side, software supply chain security firm JFrog said in an analysis published last week. The server-side weaknesses “allow attackers to…
CISA Alerts to Active Exploitation of Critical Palo Alto Networks Vulnerability
[ad_1] Nov 08, 2024Ravie LakshmananVulnerability / Network Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a now-patched critical security flaw impacting Palo Alto Networks Expedition to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerability, tracked as CVE-2024-5910 (CVSS score: 9.3), concerns a case of missing authentication…
Transforming MSPs and MSSPs into Cybersecurity Powerhouses
[ad_1] Nov 08, 2024The Hacker NewsCyber Resilience / Compliance We’ve all heard a million times: growing demand for robust cybersecurity in the face of rising cyber threats is undeniable. Globally small and medium-sized businesses (SMBs) are increasingly targeted by cyberattacks but often lack the resources for full-time Chief Information Security Officers (CISOs). This gap is…
Malicious NPM Packages Target Roblox Users with Data-Stealing Malware
[ad_1] Nov 08, 2024Ravie LakshmananOpen Source / Malware A new campaign has targeted the npm package repository with malicious JavaScript libraries that are designed to infect Roblox users with open-source stealer malware such as Skuld and Blank-Grabber. “This incident highlights the alarming ease with which threat actors can launch supply chain attacks by exploiting trust…
IcePeony and Transparent Tribe Target Indian Entities with Cloud-Based Tools
[ad_1] Nov 08, 2024Ravie LakshmananCyber Espionage / Threat Intelligence High-profile entities in India have become the target of malicious campaigns orchestrated by the Pakistan-based Transparent Tribe threat actor and a previously unknown China-nexus cyber espionage group dubbed IcePeony. The intrusions linked to Transparent Tribe involve the use of a malware called ElizaRAT and a new…