[ad_1] Oct 22, 2024Ravie LakshmananVulnerability / Cyber Threat The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a critical security flaw impacting ScienceLogic SL1 to its Known Exploited Vulnerabilities (KEV) catalog, following reports of active exploitation as a zero-day. The vulnerability in question, tracked as CVE-2024-9537 (CVSS v4 score: 9.3), refers to a…
Category: Cyber News
VMware Releases vCenter Server Update to Fix Critical RCE Vulnerability
[ad_1] Oct 22, 2024Ravie LakshmananVulnerability / Enterprise Security VMware has released software updates to address an already patched security flaw in vCenter Server that could pave the way for remote code execution. The vulnerability, tracked as CVE-2024-38812 (CVSS score: 9.8), concerns a case of heap-overflow vulnerability in the implementation of the DCE/RPC protocol. “A malicious…
CERT-UA Identifies Malicious RDP Files in Latest Attack on Ukrainian Entities
[ad_1] Oct 26, 2024Ravie LakshmananCyber Attack / Threat Intelligence The Computer Emergency Response Team of Ukraine (CERT-UA) has detailed a new malicious email campaign targeting government agencies, enterprises, and military entities. “The messages exploit the appeal of integrating popular services like Amazon or Microsoft and implementing a zero-trust architecture,” CERT-UA said. “These emails contain attachments…
Malicious npm Packages Target Developers’ Ethereum Wallets with SSH Backdoor
[ad_1] Oct 22, 2024Ravie LakshmananVulnerability / Supply Chain Cybersecurity researchers have discovered a number of suspicious packages published to the npm registry that are designed to harvest Ethereum private keys and gain remote access to the machine via the secure shell (SSH) protocol. The packages attempt to “gain SSH access to the victim’s machine by…
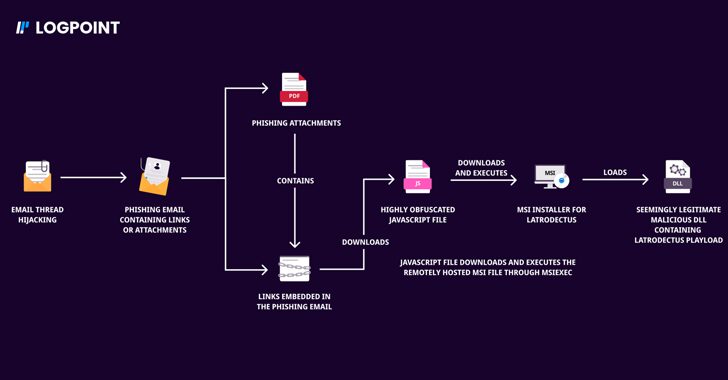
Bumblebee and Latrodectus Malware Return with Sophisticated Phishing Strategies
[ad_1] Oct 22, 2024Ravie LakshmananMalware / Threat Intelligence Two malware families that suffered setbacks in the aftermath of a coordinated law enforcement operation called Endgame have resurfaced as part of new phishing campaigns. Bumblebee and Latrodectus, which are both malware loaders, are designed to steal personal data, along with downloading and executing additional payloads onto…
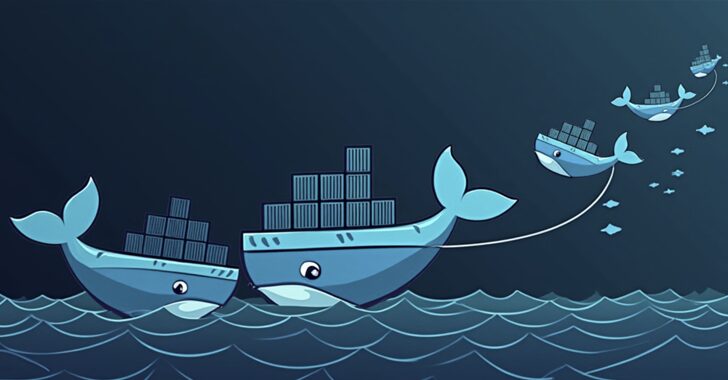
Cybercriminals Exploiting Docker API Servers for SRBMiner Crypto Mining Attacks
[ad_1] Oct 22, 2024Ravie LakshmananDocker Security / Cloud Security Bad actors have been observed targeting Docker remote API servers to deploy the SRBMiner crypto miner on compromised instances, according to new findings from Trend Micro. “In this attack, the threat actor used the gRPC protocol over h2c to evade security solutions and execute their crypto…
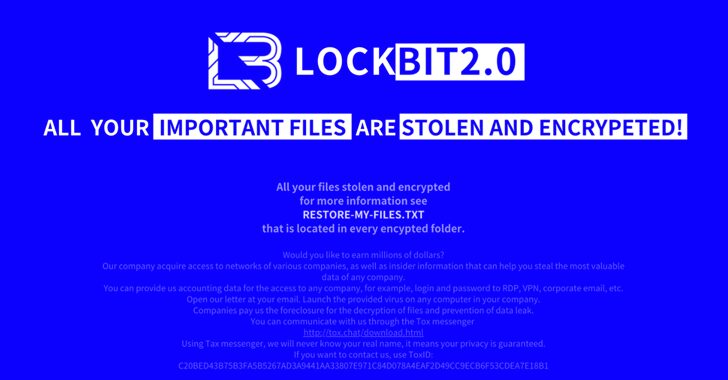
Ransomware Gangs Use LockBit’s Fame to Intimidate Victims in Latest Attacks
[ad_1] Threat actors have been observed abusing Amazon S3 (Simple Storage Service) Transfer Acceleration feature as part of ransomware attacks designed to exfiltrate victim data and upload them to S3 buckets under their control. “Attempts were made to disguise the Golang ransomware as the notorious LockBit ransomware,” Trend Micro researchers Jaromir Horejsi and Nitesh Surana…
Researchers Discover Command Injection Flaw in Wi-Fi Alliance’s Test Suite
[ad_1] Oct 25, 2024Ravie LakshmananVulnerability / Wi-Fi Security A security flaw impacting the Wi-Fi Test Suite could enable unauthenticated local attackers to execute arbitrary code with elevated privileges. The CERT Coordination Center (CERT/CC) said the vulnerability, tracked as CVE-2024-41992, said the susceptible code from the Wi-Fi Alliance has been found deployed on Arcadyan FMIMG51AX000J routers….
Apple Opens PCC Source Code for Researchers to Identify Bugs in Cloud AI Security
[ad_1] Oct 25, 2024Ravie LakshmananCloud Security / Artificial Intelligence Apple has publicly made available its Private Cloud Compute (PCC) Virtual Research Environment (VRE), allowing the research community to inspect and verify the privacy and security guarantees of its offering. PCC, which Apple unveiled earlier this June, has been marketed as the “most advanced security architecture…
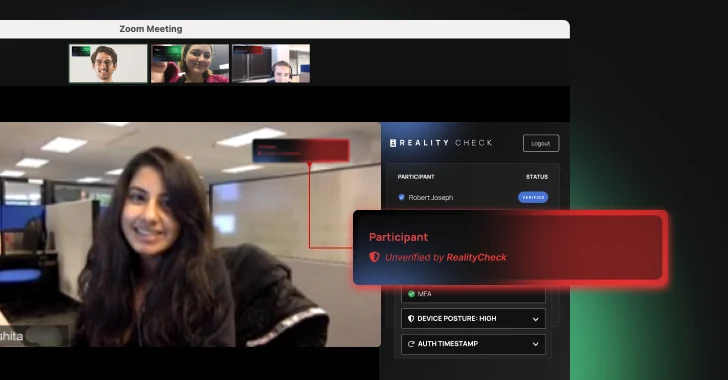
Is Your Identity Security AI-Proof?
[ad_1] Oct 25, 2024The Hacker NewsArtificial Intelligence / Identity Security Artificial Intelligence (AI) has rapidly evolved from a futuristic concept to a potent weapon in the hands of bad actors. Today, AI-based attacks are not just theoretical threats—they’re happening across industries and outpacing traditional defense mechanisms. The solution, however, is not futuristic. It turns out…