[ad_1] Oct 23, 2024The Hacker NewsIdentity Security / Data Protection Identity security is front, and center given all the recent breaches that include Microsoft, Okta, Cloudflare and Snowflake to name a few. Organizations are starting to realize that a shake-up is needed in terms of the way we approach identity security both from a strategic…
Category: Cyber News
New Grandoreiro Banking Malware Variants Emerge with Advanced Tactics to Evade Detection
[ad_1] New variants of a banking malware called Grandoreiro have been found to adopt new tactics in an effort to bypass anti-fraud measures, indicating that the malicious software is continuing to be actively developed despite law enforcement efforts to crack down on the operation. “Only part of this gang was arrested: the remaining operators behind…
Researchers Reveal ‘Deceptive Delight’ Method to Jailbreak AI Models
[ad_1] Oct 23, 2024Ravie LakshmananArtificial Intelligence / Vulnerability Cybersecurity researchers have shed light on a new adversarial technique that could be used to jailbreak large language models (LLMs) during the course of an interactive conversation by sneaking in an undesirable instruction between benign ones. The approach has been codenamed Deceptive Delight by Palo Alto Networks…
Security Flaw in Styra’s OPA Exposes NTLM Hashes to Remote Attackers
[ad_1] Oct 22, 2024Ravie LakshmananVulnerability / Software Security Details have emerged about a now-patched security flaw in Styra’s Open Policy Agent (OPA) that, if successfully exploited, could have led to leakage of New Technology LAN Manager (NTLM) hashes. “The vulnerability could have allowed an attacker to leak the NTLM credentials of the OPA server’s local…
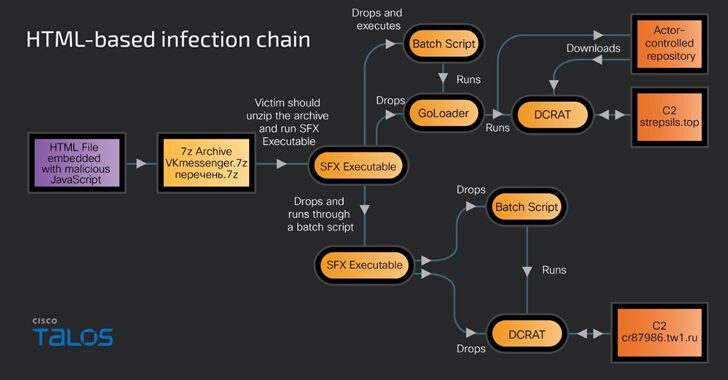
Gophish Framework Used in Phishing Campaigns to Deploy Remote Access Trojans
[ad_1] Russian-speaking users have become the target of a new phishing campaign that leverages an open-source phishing toolkit called Gophish to deliver DarkCrystal RAT (aka DCRat) and a previously undocumented remote access trojan dubbed PowerRAT. “The campaign involves modular infection chains that are either Maldoc or HTML-based infections and require the victim’s intervention to trigger…
A Comprehensive Guide to Finding Service Accounts in Active Directory
[ad_1] Oct 22, 2024Ravie LakshmananIdentity Management / Security Automation Service accounts are vital in any enterprise, running automated processes like managing applications or scripts. However, without proper monitoring, they can pose a significant security risk due to their elevated privileges. This guide will walk you through how to locate and secure these accounts within Active…
Guide: The Ultimate Pentest Checklist for Full-Stack Security
[ad_1] Oct 21, 2024The Hacker NewsPenetration Testing / API Security Pentest Checklists Are More Important Than Ever Given the expanding attack surface coupled with the increasing sophistication of attacker tactics and techniques, penetration testing checklists have become essential for ensuring thorough assessments across an organization’s attack surface, both internal and external. By providing a structured…
Chinese Nation-State Hackers APT41 Hit Gambling Sector for Financial Gain
[ad_1] The prolific Chinese nation-state actor known as APT41 (aka Brass Typhoon, Earth Baku, Wicked Panda, or Winnti) has been attributed to a sophisticated cyber attack targeting the gambling and gaming industry. “Over a period of at least six months, the attackers stealthily gathered valuable information from the targeted company including, but not limited to,…
Researchers Discover Severe Security Flaws in Major E2EE Cloud Storage Providers
[ad_1] Oct 21, 2024Ravie LakshmananEncryption / Data Protection Cybersecurity researchers have discovered severe cryptographic issues in various end-to-end encrypted (E2EE) cloud storage platforms that could be exploited to leak sensitive data. “The vulnerabilities range in severity: in many cases a malicious server can inject files, tamper with file data, and even gain direct access to…
5 Ways to Reduce SaaS Security Risks
[ad_1] As technology adoption has shifted to be employee-led, just in time, and from any location or device, IT and security teams have found themselves contending with an ever-sprawling SaaS attack surface, much of which is often unknown or unmanaged. This greatly increases the risk of identity-based threats, and according to a recent report from…