[ad_1]
The threat actor known as Dark Caracal has been attributed to a campaign that deployed a remote access trojan called Poco RAT in attacks targeting Spanish-speaking targets in Latin America in 2024.
The findings come from Russian cybersecurity company Positive Technologies, which described the malware as loaded with a “full suite of espionage features.”
“It could upload files, capture screenshots, execute commands, and manipulate system processes,” researchers Denis Kazakov and Sergey Samokhin said in a technical report published last week.
Poco RAT was previously documented by Cofense in July 2024, detailing the phishing attacks aimed at mining, manufacturing, hospitality, and utilities sectors. The infection chains are characterized by the use of finance-themed lures that trigger a multi-step process to deploy the malware.
While the campaign was not attributed to any threat at that time, Positive Technologies said it identified tradecraft overlaps with Dark Caracal, an advanced persistent threat (APT) known for operating malware families like CrossRAT and Bandook. It’s operational since at least 2012.
In 2021, the cyber mercenary group was tied to a cyber espionage campaign dubbed Bandidos that delivered an updated version of the Bandook malware against Spanish-speaking countries in South America.
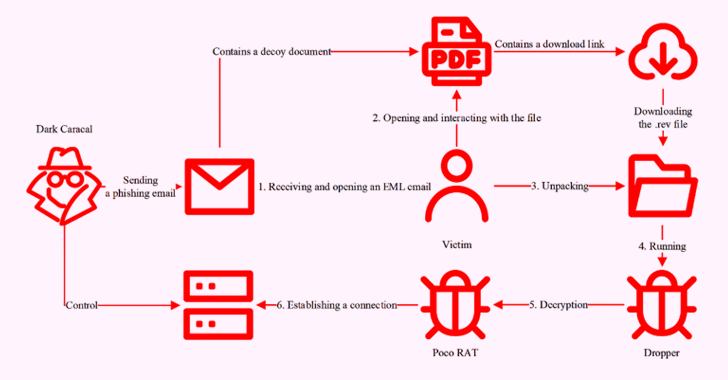
The latest set of attacks continue their focus on Spanish-speaking users, leveraging phishing emails with invoice-related themes that bear malicious attachments written in Spanish as a starting point. An analysis of Poco RAT artifacts indicates the intrusions are mainly targeting enterprises in Venezuela, Chile, the Dominican Republic, Colombia, and Ecuador.
The attached decoy documents impersonate a wide range of industry verticals, including banking, manufacturing, healthcare, pharmaceuticals, and logistics, in an attempt to lend the scheme a little more believability.
When opened, the files redirect victims to a link that triggers the download of a .rev archive from legitimate file-sharing services or cloud storage platforms like Google Drive and Dropbox.
“Files with the .rev extension are generated using WinRAR and were originally designed to reconstruct missing or corrupted volumes in multi-part archives,” the researchers explained. “Threat actors repurpose them as stealthy payload containers, helping malware evade security detection.”
Present within the archive is a Delphi-based dropper that’s responsible for launching Poco RAT, which, in turn, establishes contact with a remote server and grants attackers full control over compromised hosts. The malware gets its name from the use of POCO libraries in its C++ codebase.
Some of the supported commands by Poco RAT are listed below –
- T-01 – Send collected system data to the command-and-control (C2) server
- T-02 – Retrieve and transmit the active window title to the C2 server
- T-03 – Download and run an executable file
- T-04 – Download a file to the compromised machine
- T-05 – Capture a screenshot and send it to the C2 server
- T-06 – Execute a command in cmd.exe and send the output to the C2 server
“Poco RAT does not come with a built-in persistence mechanism,” the researchers said. “Once initial reconnaissance is complete, the server likely issues a command to establish persistence, or attackers may use Poco RAT as a stepping stone to deploy the primary payload.”
[ad_2]