[ad_1]
The threat actor known as EncryptHub exploited a recently-patched security vulnerability in Microsoft Windows as a zero-day to deliver a wide range of malware families, including backdoors and information stealers such as Rhadamanthys and StealC.
“In this attack, the threat actor manipulates .msc files and the Multilingual User Interface Path (MUIPath) to download and execute malicious payload, maintain persistence and steal sensitive data from infected systems,” Trend Micro researcher Aliakbar Zahravi said in an analysis.
The vulnerability in question is CVE-2025-26633 (CVSS score: 7.0), described by Microsoft as an improper neutralization vulnerability in Microsoft Management Console (MMC) that could allow an attacker to bypass a security feature locally. It was fixed by the company earlier this month as part of its Patch Tuesday update.
Trend Micro has given the exploit the moniker MSC EvilTwin, tracking the suspected Russian activity cluster under the name Water Gamayun. The threat actor, recently the subject of analyses by PRODAFT and Outpost24, is also called LARVA-208.
CVE-2025-26633, at its core, leverages the Microsoft Management Console framework (MMC) to execute a malicious Microsoft Console (.msc) file by means of a PowerShell loader referred to as MSC EvilTwin loader.
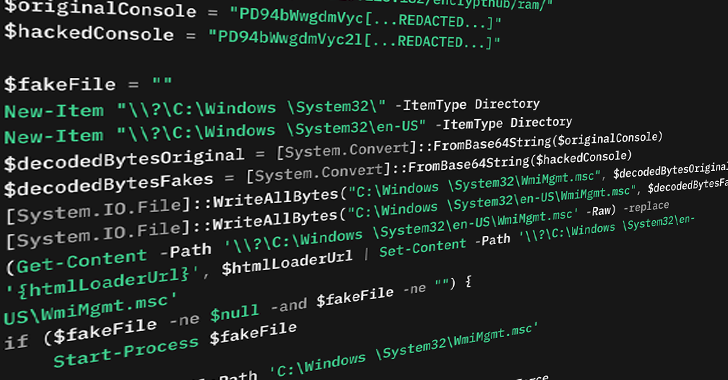
Specifically, it involves the loader creating two .msc files with the same name: One clean file and its rogue counterpart that is dropped in the same location but within a directory named “en-US.” The idea is that when the former is run, MMC inadvertently picks the malicious file instead and executes it. This is accomplished by exploiting MMC’s Multilingual User Interface Path (MUIPath) feature.
“By abusing the way that mmc.exe uses MUIPath, the attacker can equip MUIPath en-US with a malicious .msc file, which cause the mmc.exe load this malicious file instead of the original file and executed without the victim’s knowledge,” Zahravi explained.
EncryptHub has also been observed adopting two other methods to run malicious payload on an infected system using .msc files –
- Using the ExecuteShellCommand method of MMC to download and execute a next-stage payload on the victim’s machine, an approach previously documented by Dutch cybersecurity company Outflank in August 2024
- Using mock trusted directories such as “C:\Windows \System32” (note the space after Windows) to bypass User Account Control (UAC) and drop a malicious .msc file called “WmiMgmt.msc”
Trend Micro said the attack chains likely begin with victims downloading digitally-signed Microsoft installer (MSI) files impersonating legitimate Chinese software like DingTalk or QQTalk, which is then used to fetch and execute the loader from a remote server. It’s said that the threat actor has been experimenting with these techniques since April 2024.
“This campaign is under active development; it employs multiple delivery methods and custom payloads designed to maintain persistence and steal sensitive data, then exfiltrate it to the attackers’ command-and-control (C&C) servers,” Zahravi said.
[ad_2]