[ad_1]
A number of state-back threat actors from Russia and China have been observed exploiting a recent security flaw in the WinRAR archiver tool for Windows as part of their operations.
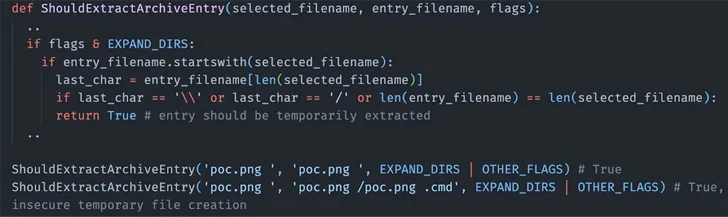
The vulnerability in question is CVE-2023-38831 (CVSS score: 7.8), which allows attackers to execute arbitrary code when a user attempts to view a benign file within a ZIP archive. The shortcoming has been actively exploited since at least April 2023.
Google Threat Analysis Group (TAG), which detected the activities in recent weeks, attributed them to three different clusters it tracks under the geological monikers FROZENBARENTS (aka Sandworm), FROZENLAKE (aka APT28), and ISLANDDREAMS (aka APT40).
The phishing attack linked to Sandworm impersonated a Ukrainian drone warfare training school in early September and distributed a malicious ZIP file exploiting CVE-2023-38831 to deliver Rhadamanthys, a commodity stealer malware which is offered for sale for $250 for a monthly subscription.
APT28, also affiliated with the Main Directorate of the General Staff of the Armed Forces of the Russian Federation (GRU) as it’s the case with Sandworm, is said to have launched an email campaign targeting government organizations in Ukraine.
In these attacks, users from Ukraine were prompted to download a file containing a CVE-2023-38831 exploit – a decoy document that masqueraded as an event invitation from Razumkov Centre, a public policy think tank in the country.
The result is the execution of a PowerShell script named IRONJAW that steals browser login data and local state directories and exports the information to an actor-controlled infrastructure on webhook[.]site.
The third threat actor to exploit the WinRAR bug is APT40, which unleashed a phishing campaign targeting Papua New Guinea in which the email messages included a Dropbox link to a ZIP archive containing the CVE-2023-38831 exploit.
The infection sequence ultimately paved the way for the deployment of a dropper named ISLANDSTAGER that’s responsible for loading BOXRAT, a .NET backdoor that uses the Dropbox API for command-and-control
The disclosure builds upon recent findings from Cluster25, which detailed attacks undertaken by the APT28 hacking crew exploiting the WinRAR flaw to conduct credential harvesting operations.
Some of the other state-sponsored adversaries that have joined the fray are Konni (which shares overlaps with a North Korean cluster tracked as Kimsuky) and Dark Pink (aka Saaiwc Group), according to findings from the Knownsec 404 team and NSFOCUS.
“The widespread exploitation of the WinRAR bug highlights that exploits for known vulnerabilities can be highly effective, despite a patch being available,” TAG researcher
Kate Morgan said. “Even the most sophisticated attackers will only do what is necessary to accomplish their goals.”
[ad_2]