[ad_1]
A proof-of-concept (PoC) exploit has been released for a now-patched security flaw impacting Windows Lightweight Directory Access Protocol (LDAP) that could trigger a denial-of-service (DoS) condition.
The out-of-bounds reads vulnerability is tracked as CVE-2024-49113 (CVSS score: 7.5). It was addressed by Microsoft as part of Patch Tuesday updates for December 2024, alongside CVE-2024-49112 (CVSS score: 9.8), a critical integer overflow flaw in the same component that could result in remote code execution.
Credited with discovering and reporting both vulnerabilities is independent security researcher Yuki Chen (@guhe120).
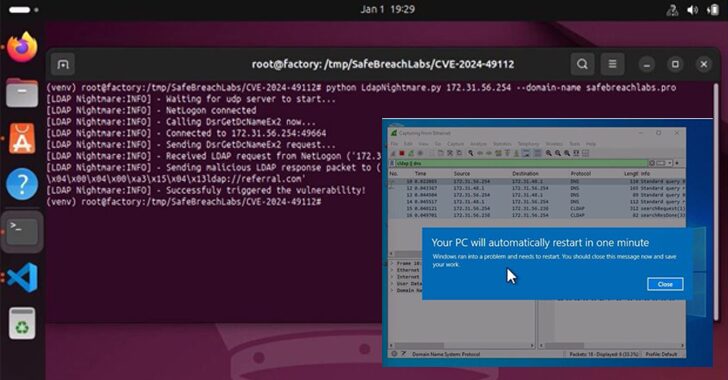
The CVE-2024-49113 PoC devised by SafeBreach Labs, codenamed LDAPNightmare, is designed to crash any unpatched Windows Server “with no pre-requisites except that the DNS server of the victim DC has Internet connectivity.”
Specifically, it entails sending a DCE/RPC request to the victim server, ultimately causing the Local Security Authority Subsystem Service (LSASS) to crash and force a reboot when a specially crafted CLDAP referral response packet.
Even worse, the California-based cybersecurity company found that the same exploit chain could also be leveraged to achieve remote code execution (CVE-2024-49112) by modifying the CLDAP packet.
Microsoft’s advisory for CVE-2024-49113 is lean on technical details, but the Windows maker has revealed that CVE-2024-49112 could be exploited by sending RPC requests from untrusted networks to execute arbitrary code within the context of the LDAP service.
“In the context of exploiting a domain controller for an LDAP server, to be successful an attacker must send specially crafted RPC calls to the target to trigger a lookup of the attacker’s domain to be performed in order to be successful,” Microsoft said.
“In the context of exploiting an LDAP client application, to be successful an attacker must convince or trick the victim into performing a domain controller lookup for the attacker’s domain or into connecting to a malicious LDAP server. However, unauthenticated RPC calls would not succeed.”
Furthermore, an attacker could use an RPC connection to a domain controller to trigger domain controller lookup operations against the attacker’s domain, the company noted.
To mitigate the risk posed by these vulnerabilities, it’s essential that organizations apply the December 2024 patches released by Microsoft. In situations where immediate patching is not possible, it’s advised to “implement detections to monitor suspicious CLDAP referral responses (with the specific malicious value set), suspicious DsrGetDcNameEx2 calls, and suspicious DNS SRV queries.”
[ad_2]