[ad_1]
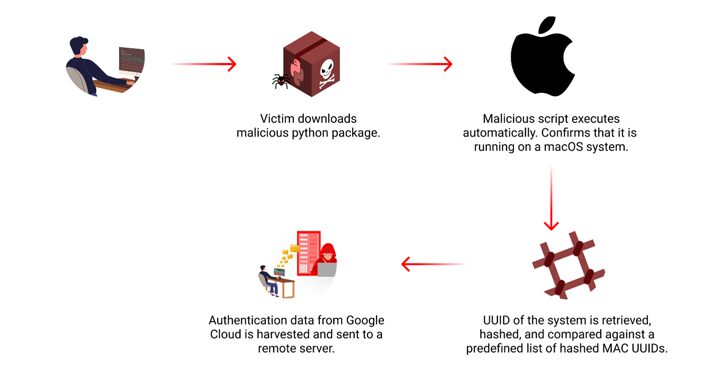
Cybersecurity researchers have discovered a malicious package on the Python Package Index (PyPI) repository that targets Apple macOS systems with the goal of stealing users’ Google Cloud credentials from a narrow pool of victims.
The package, named “lr-utils-lib,” attracted a total of 59 downloads before it was taken down. It was uploaded to the registry in early June 2024.
“The malware uses a list of predefined hashes to target specific macOS machines and attempts to harvest Google Cloud authentication data,” Checkmarx researcher Yehuda Gelb said in a Friday report. “The harvested credentials are sent to a remote server.”

An important aspect of the package is that it first checks if it has been installed on a macOS system, and only then proceeds to compare the system’s Universally Unique Identifier (UUID) against a hard-coded list of 64 hashes.
If the compromised machine is among those specified in the predefined set, it attempts to access two files, namely application_default_credentials.json and credentials.db, located in the ~/.config/gcloud directory, which contain Google Cloud authentication data.
The captured information is then transmitted over HTTP to a remote server “europe-west2-workload-422915[.]cloudfunctions[.]net.”
Checkmarx said it also found a fake profile on LinkedIn with the name “Lucid Zenith” that matched the package’s owner and falsely claimed to be the CEO of Apex Companies, suggesting a possible social engineering element to the attack.
Exactly who is behind the campaign is currently not known. However, it comes more than two months after cybersecurity firm Phylum disclosed details of another supply chain attack involving a Python package called “requests-darwin-lite” that was also found to unleash its malicious actions after checking the UUID of the macOS host.
These campaigns are a sign that threat actors have prior knowledge of the macOS systems they want to infiltrate and are going to great lengths to ensure that the malicious packages are distributed only to those particular machines.
It also speaks to the tactics malicious actors employ to distribute lookalike packages, aiming to deceive developers into incorporating them into their applications.
“While it is not clear whether this attack targeted individuals or enterprises, these kinds of attacks can significantly impact enterprises,” Gelb said. “While the initial compromise usually occurs on an individual developer’s machine, the implications for enterprises can be substantial.”
[ad_2]