[ad_1]
Threat actors are exploiting a novel attack technique in the wild that leverages specially crafted management saved console (MSC) files to gain full code execution using Microsoft Management Console (MMC) and evade security defenses.
Elastic Security Labs has codenamed the approach GrimResource after identifying an artifact (“sccm-updater.msc“) that was uploaded to the VirusTotal malware scanning platform on June 6, 2024.
“When a maliciously crafted console file is imported, a vulnerability in one of the MMC libraries can lead to running adversary code, including malware,” the company said in a statement shared with The Hacker News.
“Attackers can combine this technique with DotNetToJScript to gain arbitrary code execution, which can lead to unauthorized access, system takeover and more.”
The use of uncommon file types as a malware distribution vector is seen as an alternative attempt by adversaries to get around security guardrails erected by Microsoft in recent years, including disabling macros by default in Office files downloaded from the internet.
Last month, South Korean cybersecurity firm Genians detailed the use of a malicious MSC file by the North Korea-linked Kimsuky hacking group to deliver malware.
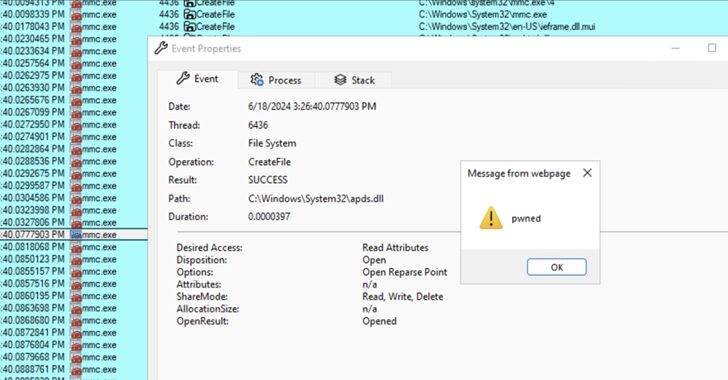
GrimResource, on the other hand, exploits a cross-site scripting (XSS) flaw present in the apds.dll library to execute arbitrary JavaScript code in the context of MMC. The XSS flaw was originally reported to Microsoft and Adobe in late 2018, although it remains unpatched to date.
This is accomplished by adding a reference to the vulnerable APDS resource in the StringTable section of a malicious MSC file, which, when opened using MMC, triggers the execution of JavaScript code.

The technique not only bypasses ActiveX warnings, it can be combined with DotNetToJScript to gain arbitrary code execution. The analyzed sample uses this approach to launch a .NET loader component dubbed PASTALOADER that ultimately paves the way for Cobalt Strike.
“After Microsoft disabled Office macros by default for internet-sourced documents, other infection vectors like JavaScript, MSI files, LNK objects, and ISOs have surged in popularity,” security researchers Joe Desimone and Samir Bousseaden said.
“However, these other techniques are scrutinized by defenders and have a high likelihood of detection. Attackers have developed a new technique to execute arbitrary code in Microsoft Management Console using crafted MSC files.”
[ad_2]