[ad_1]
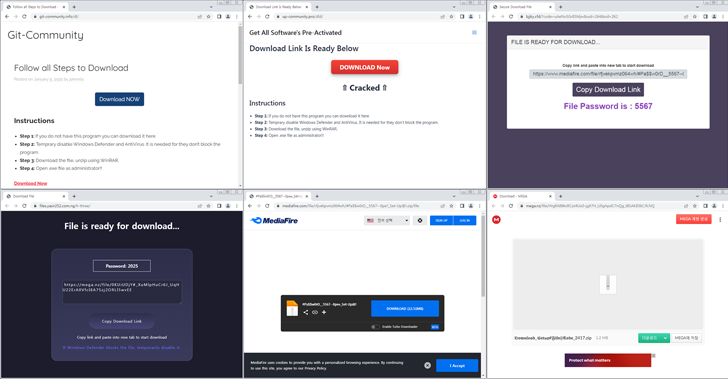
Cybersecurity researchers are warning of a new campaign that leverages cracked versions of software as a lure to distribute information stealers like Lumma and ACR Stealer.
The AhnLab Security Intelligence Center (ASEC) said it has observed a spike in the distribution volume of ACR Stealer since January 2025.
A notable aspect of the stealer malware is the use of a technique called dead drop resolver to extract the actual command-and-control (C2) server. This includes relying on legitimate services like Steam, Telegram’s Telegraph, Google Forms, and Google Slides.
“Threat actors enter the actual C2 domain in Base64 encoding on a specific page,” ASEC said. “The malware accesses this page, parses the string, and obtains the actual C2 domain address to perform malicious behaviors.”
ACR Stealer, previously distributed via Hijack Loader malware, is capable of harvesting a wide range of information from compromised systems, including files, web browser data, and cryptocurrency wallet extensions.
The development comes as ASEC revealed another campaign that uses files with the extension “MSC,” which can be executed by the Microsoft Management Console (MMC), to deliver the Rhadamanthys stealer malware.
“There are two types of MSC malware: one exploits the vulnerability of apds.dll (CVE-2024-43572), and the other executes the ‘command’ command using Console Taskpad,” the South Korean company said.
“The MSC file is disguised as an MS Word document. “When the ‘Open’ button is clicked, it downloads and executes a PowerShell script from an external source. The downloaded PowerShell script contains an EXE file (Rhadamanthys).”
CVE-2024-43572, also called GrimResource, was first documented by the Elastic Security Labs in June 2024 as having been exploited by malicious actors as a zero-day. It was patched by Microsoft in October 2024.
Malware campaigns have also been observed exploiting chat support platforms like Zendesk, masquerading as customers to trick unsuspecting support agents into downloading a stealer called Zhong Stealer.
According to a recent report published by Hudson Rock, over 30,000,000 computers have been infected by information stealers in the “past few years,” leading to the theft of corporate credentials and session cookies that could then be sold by cybercriminals on underground forums to other actors for profit.
The buyers could weaponize the access afforded by these credentials to stage post-exploitation actions of their own, leading to severe risks. These developments serve to highlight the role played by stealer malware as an initial access vector that provides a foothold to sensitive corporate environments.
“For as little as $10 per log (computer), cybercriminals can purchase stolen data from employees working in classified defense and military sectors,” Hudson Rock said. “Infostealer intelligence isn’t just about detecting who’s infected — it’s about understanding the full network of compromised credentials and third-party risks.”
Over the past year, threat actors have also been ramping up efforts to spread a variety of malware families, including stealers and remote access trojans (RATs), through a technique called ClickFix that often entails redirecting users to fake CAPTCHA verification pages instructing them to copy and execute nefarious PowerShell commands.
One such payload dropped is I2PRAT, which employs the I2P anonymization network to anonymize its final C2 server.
“The malware is an advanced threat composed of multiple layers, each incorporating sophisticated mechanisms,” Sekoia said. “The use of an anonymization network complicates tracking and hinders the identification of the threat’s magnitude and spread in the wild.”
[ad_2]