[ad_1]
Threat actors have been found leveraging a new technique that abuses extended attributes for macOS files to smuggle a new malware called RustyAttr.
The Singaporean cybersecurity company has attributed the novel activity with moderate confidence to the infamous North Korea-linked Lazarus Group, citing infrastructure and tactical overlaps observed in connection with prior campaigns, including RustBucket.
Extended attributes refer to additional metadata associated with files and directories that can be extracted using a dedicated command called xattr. They are often used to store information that goes beyond the standard attributes, such as file size, timestamps, and permissions.
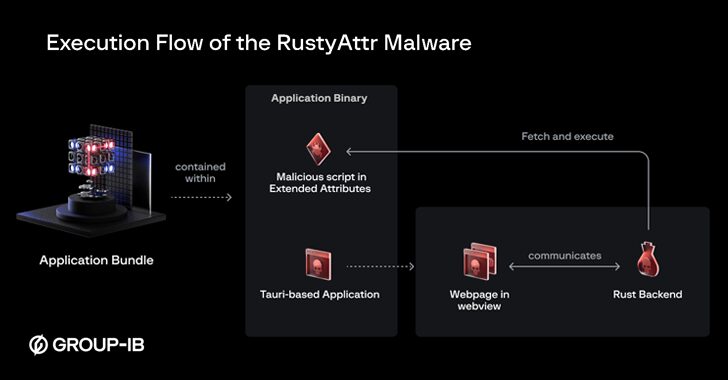
The malicious applications discovered by Group-IB are built using Tauri, a cross-platform desktop application framework, and signed with a leaked certificate that has since been revoked by Apple. They include an extended attribute that’s configured to fetch and run a shell script.
The execution of the shell script also triggers a decoy, which serves as a distraction mechanism by either displaying an error message “This app does not support this version” or a seemingly harmless PDF document related to the development and funding of gaming projects.
“Upon executing the application, the Tauri application attempts to render a HTML webpage using a WebView,” Group-IB security researcher Sharmine Low said. “The [threat actor] used some random template pulled off the internet.”
But what’s also notable is that these web pages are engineered to load a malicious JavaScript, which then obtains the content of the extended attributes and executes it by means of a Rust backend. That said, the fake web page is eventually displayed only in cases where there are no extended attributes.
The end goal of the campaign remains unclear, especially in light of the fact that there has been no evidence of any further payloads or confirmed victims.
“Fortunately, macOS systems provide some level of protection for the found samples,” Low said. “To trigger the attack, users must disable Gatekeeper by overriding malware protection. It is likely that some degree of interaction and social engineering will be necessary to convince victims to take these steps.”
The development comes as North Korean threat actors have been engaging in extensive campaigns that aim to secure remote positions with businesses across the world, as well as trick current employees working at cryptocurrency companies into downloading malware under the pretext of coding interviews.
[ad_2]