No Blind Spots: A Veteran’s Blueprint to Protect Critical Infrastructure
Cybersecurity blind spots are the cracks where attacks slip through—threatening your critical infrastructure and national security. You might think your OT and IT environments are locked down, but hidden gaps in asset visibility, third-party risk, and leadership processes keep exposing you. This post lays out a veteran’s blueprint to close those gaps with military precision, 360-degree visibility, and zero trust for OT. Ready to secure your mission and master actionable defense? Learn more about how hidden blind spots quietly became cybersecurity’s biggest.
Identifying Cybersecurity Blind Spots
Even seasoned leaders can overlook hidden cybersecurity gaps. These blind spots pose threats to crucial infrastructure. Addressing them is essential for robust protection.
Gaps in OT/IT Convergence
Operational Technology (OT) and Information Technology (IT) often operate in silos. This separation creates unseen vulnerabilities. You might think your systems are integrated, but are they truly working together?
-
Communication Breakdown: The lack of communication between OT and IT teams can lead to missed threats. Ensure regular cross-functional meetings to bridge this gap.
-
Interoperability Issues: Systems that don’t communicate effectively can create blind spots. Use compatible technology to improve connectivity.
-
Security Protocols Mismatch: OT and IT might have different security measures. Align these protocols to ensure comprehensive protection. For more on improving network visibility to prevent blind spots, check out this resource.
Third-Party Exposure Risks
Third-party vendors are often overlooked in security audits. These partners can become gateways for attacks. Do you know how secure your vendors are?
-
Vendor Assessment: Regularly assess your vendors’ security protocols. Use a standardized checklist to streamline this process.
-
Access Controls: Limit vendor access to only necessary data and systems. Implement multi-factor authentication for added security.
-
Contractual Obligations: Clearly define security expectations in contracts. Hold vendors accountable for breaches. For insights on advancing risk maturity to close federal cybersecurity blind spots, explore this article.
Building a Resilient Defense Framework
A robust defense framework is key to cybersecurity. Let’s explore ways to establish complete visibility and Zero Trust in your systems.
Establishing 360-Degree Asset Visibility
Full asset visibility is non-negotiable. Without it, you can’t protect what you can’t see. Here’s how to ensure you have eyes on everything.
-
Asset Inventory: Document all assets, both digital and physical. This includes software, hardware, and network components.
-
Continuous Monitoring: Implement tools that provide real-time updates on asset status. This helps in identifying unauthorized changes promptly.
-
Regular Audits: Conduct periodic audits to verify asset records. This ensures that your inventory is always current. Learn more about reducing cyber threats in operational technology with primary mitigations here.
Engineering Zero Trust for OT
Zero Trust is a vital strategy for OT security. It assumes that threats are already inside your network. How can you implement Zero Trust effectively?
-
Identity Verification: Always verify user identities before granting access. Use robust methods like biometric authentication.
-
Network Segmentation: Divide your network into smaller segments. This limits the movement of potential threats within your system.
-
Least Privilege Principle: Grant users the minimum access necessary for their roles. Regularly review and adjust access levels.
Strengthening Cybersecurity Culture and Training
Your defense is only as strong as your weakest link. Build a culture that prioritizes security and continuous learning.
Hardening the Human Layer
Humans are often the weakest link in cybersecurity. Strengthening this layer is crucial. How can you ensure your team is your strongest defense?
-
Regular Training: Conduct frequent security training sessions. Cover topics like phishing and social engineering.
-
Awareness Campaigns: Launch campaigns to keep security top of mind. Use posters, emails, and workshops to reinforce best practices.
-
Behavioral Monitoring: Use tools to monitor user behavior for anomalies. Address unusual patterns promptly.
Conducting Incident Response Tabletop Exercises
Practice makes perfect. Tabletop exercises prepare your team for real incidents. Are you regularly rehearsing your response plans?
-
Scenario Planning: Develop realistic scenarios that your team might face. This can range from data breaches to ransomware attacks.
-
Role Assignments: Clearly define roles and responsibilities. Each team member should know their part in the response plan.
-
Debriefing Sessions: After each exercise, hold a debriefing session. Discuss what went well and areas for improvement.
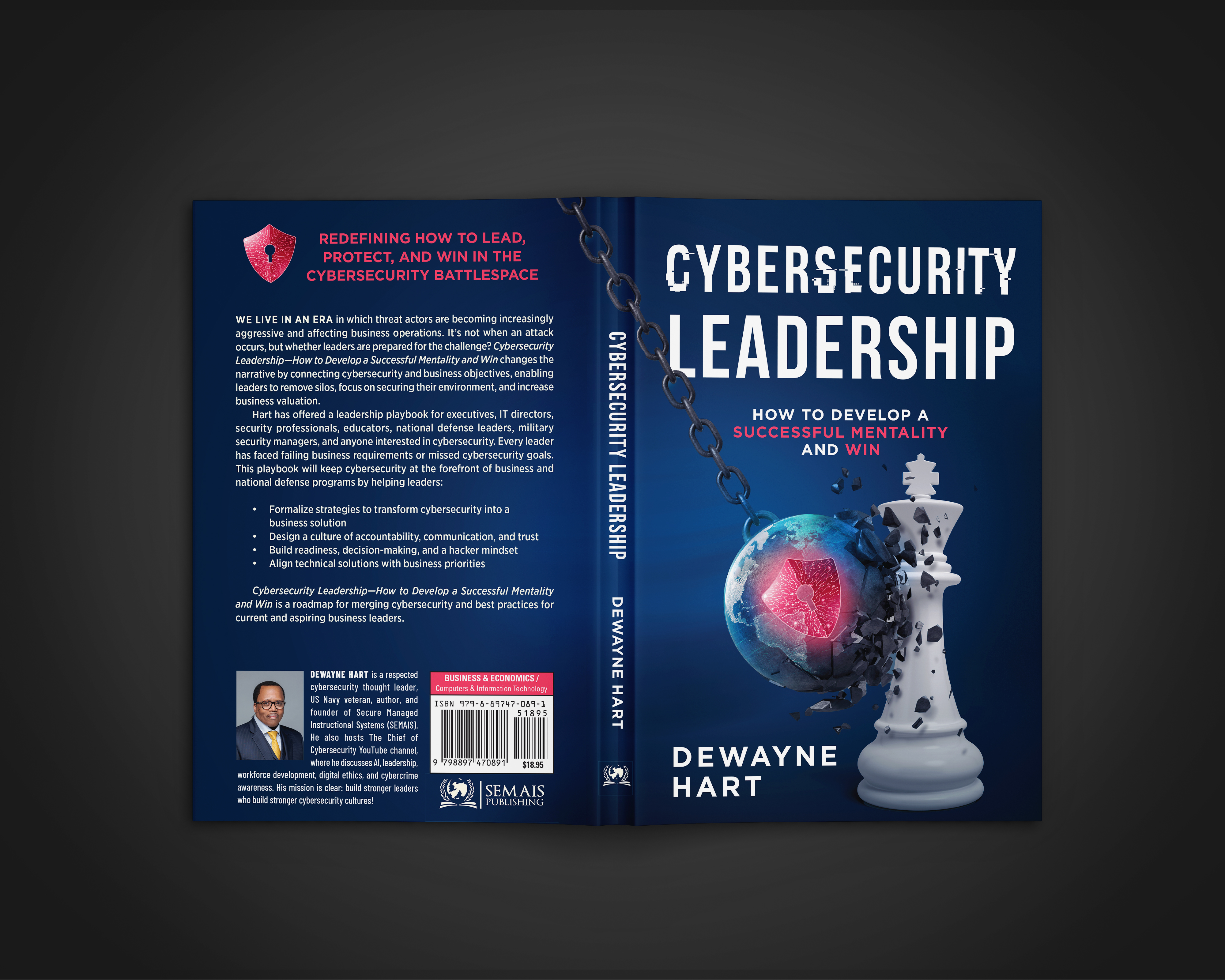
By addressing these blind spots and enhancing your security framework, you can safeguard your infrastructure against evolving threats. For further insights, explore Dewayne Hart’s books and services to fortify your cybersecurity strategy.


