[ad_1]
A financially motivated threat actor has been linked to an ongoing phishing email campaign that has been ongoing since at least July 2024 specifically targeting users in Poland and Germany.
The attacks have led to the deployment of various payloads, such as Agent Tesla, Snake Keylogger, and a previously undocumented backdoor dubbed TorNet that’s delivered by means of PureCrypter. TorNet is so named owing to the fact that it allows the threat actor to communicate with the victim machine over the TOR anonymity network.
“The actor is running a Windows scheduled task on victim machines—including on endpoints with a low battery—to achieve persistence,” Cisco Talos researcher Chetan Raghuprasad said in an analysis published today.
“The actor also disconnects the victim machine from the network before dropping the payload and then connects it back to the network, allowing them to evade detection by cloud antimalware solutions.”
The starting point of the attacks is a phishing email bearing fake money transfer confirmations or order receipts, with the threat actor masquerading as financial institutions and manufacturing and logistics companies. Attached to these messages are files with the extension “.tgz” in a likely attempt to evade detection.
Opening the compressed email attachment and extracting the archive contents leads to the execution of a .NET loader that, in turn, downloads and runs PureCrypter directly in memory.
The PureCrypter malware then proceeds to launch the TorNet backdoor, but not before performing a series of anti-debugger, anti-analysis, anti-VM, and anti-malware checks on the victim machine to fly under the radar.
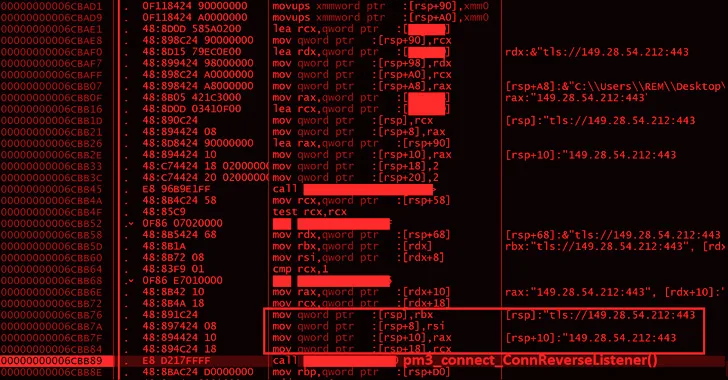
“The TorNet backdoor establishes connection to the C2 server and also connects the victim machine to the TOR network,” Raghuprasad noted. “It has the capabilities to receive and run arbitrary .NET assemblies in the victim machine’s memory, downloaded from the C2 server, increasing the attack surface for further intrusions.”
The disclosure comes days after the threat intelligence firm said it observed a surge in email threats leveraging hidden text salting in the second half of 2024 with an intent to sidestep brand name extraction by email parsers and detection engines.
“Hidden text salting is a simple yet effective technique for bypassing email parsers, confusing spam filters, and evading detection engines that rely on keywords,” security researcher Omid Mirzaei said. “The idea is to include some characters into the HTML source of an email that are not visually recognizable.”
To counter such attacks, it’s recommended to develop advanced filtering techniques that can detect hidden text salting and content concealment, including detecting use of CSS properties like “visibility” and “display,” and adopt visual similarity detection approach (e.g., Pisco) to enhance detection capabilities.
[ad_2]