[ad_1]
A new Android malware-as-a-service (MaaS) platform named SuperCard X can facilitate near-field communication (NFC) relay attacks, enabling cybercriminals to conduct fraudulent cashouts.
The active campaign is targeting customers of banking institutions and card issuers in Italy with an aim to compromise payment card data, fraud prevention firm Cleafy said in an analysis. There is evidence to suggest that the service is promoted on Telegram channels.
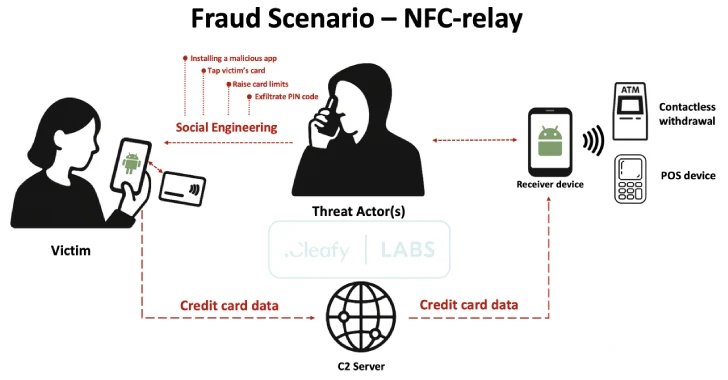
SuperCard X “employs a multi-stage approach combining social engineering (via smishing and phone calls), malicious application installation, and NFC data interception for highly effective fraud,” security researchers Federico Valentini, Alessandro Strino, and Michele Roviello said.
The new Android malware, the work of a Chinese-speaking threat actor, has been observed being propagated via three different bogus apps, duping victims into installing them via social engineering techniques like deceptive SMS or WhatsApp messages –
- Verifica Carta (io.dxpay.remotenfc.supercard11)
- SuperCard X (io.dxpay.remotenfc.supercard)
- KingCard NFC (io.dxpay.remotenfc.supercard)
The messages impersonate bank security alerts to induce a false sense of urgency by urging recipients to call a specific number to dispute the transaction.
The infection chain then moves to what’s called a Telephone-Oriented Attack Delivery (TOAD), where the threat actors manipulate victims to install the app under the guise of security software through direct phone conversations. The threat actors have also been found to employ persuasive tactics to glean victims’ PINs and instruct them to remove any existing card limits, thereby allowing them to drain the funds easily.
At the core of the operation is a previously undocumented NFC relay technique that enables threat actors to fraudulently authorize point-of-sale (PoS) payments and Automated Teller Machine (ATM) withdrawals by intercepting and relaying NFC communications from infected devices.
To do this, the attackers urge the victims to bring their debit or credit card in close physical proximity to their mobile device, which then allows the SuperCard X malware to stealthily capture the transmitted card details and relay them to an external server. The harvested card information is then utilized on a threat actor-controlled device to conduct unauthorized transactions.
The application that’s distributed to victims for capturing NFC card data is called a Reader. A similar app known as Tapper is installed on the threat actor’s device to receive the card information. Communication between the Reader and Tapper is carried out using HTTP for command-and-control (C2) and requires cybercriminals to be logged in.
As a result, threat actors are expected to create an account within the SuperCard X platform before distributing the malicious apps, after which the victims are instructed to enter the login credentials provided to them during the phone call.
This step serves as a key cog in the overall attack as it establishes the link between the victim’s infected device and the threat actor’s Tapper instance, which then enables the card data to be relayed for subsequent cash outs. The Tapper app is also designed to emulate the victim’s card using the stolen data, thus fooling PoS terminals and ATMs into recognizing it as a legitimate card.
The “Reader” malware artifacts identified by Cleafy carry subtle differences in the login screen, indicating that they are custom builds generated by affiliate actors to tailor the campaigns according to their needs. In addition, SuperCard X makes use of mutual TLS (mTLS) to secure communication with its C2 infrastructure.
That threat actors could deceive unsuspecting users into altering critical settings over phone calls hasn’t gone unnoticed by Google, which is said to be working on a new Android feature that effectively blocks users from installing apps from unknown sources and granting permissions to accessibility services.
While there is currently no evidence that SuperCard X is distributed via the Google Play Store, users are advised to scrutinize app descriptions, permissions, and reviews before downloading them. It’s also recommended to keep Google Play Protect enabled to safeguard devices against emerging threats.
“This novel campaign introduces a significant financial risk that extends beyond the conventional targets of banking institutions to affect payment providers and credit card issuers directly,” the researchers said.
“The innovative combination of malware and NFC relay empowers attackers to perform fraudulent cash-outs with debit and credit cards. This method demonstrates high efficacy, especially when targeting contactless ATM withdrawals.”
[ad_2]