[ad_1] In today’s digital world, where connectivity is rules all, endpoints serve as the gateway to a business’s digital kingdom. And because of this, endpoints are one of hackers’ favorite targets. According to the IDC, 70% of successful breaches start at the endpoint. Unprotected endpoints provide vulnerable entry points to launch devastating cyberattacks. With IT…
Month: April 2024
DOJ Arrests Founders of Crypto Mixer Samourai for $2 Billion in Illegal Transactions
[ad_1] Apr 25, 2024NewsroomCryptocurrency / Cybercrime The U.S. Department of Justice (DoJ) on Wednesday announced the arrest of two co-founders of a cryptocurrency mixer called Samourai and seized the service for allegedly facilitating over $2 billion in illegal transactions and for laundering more than $100 million in criminal proceeds. To that end, Keonne Rodriguez, 35,…
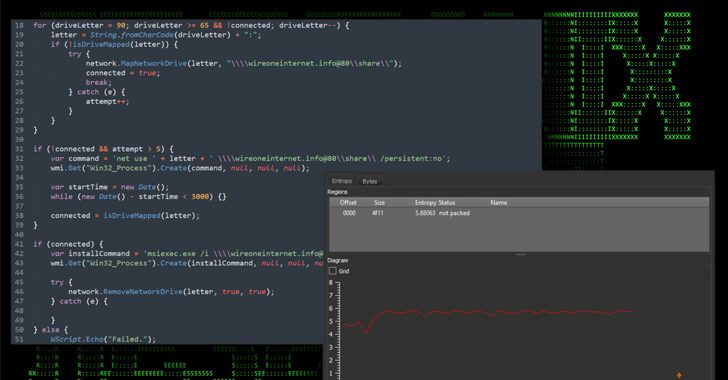
North Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
[ad_1] Apr 25, 2024NewsroomMalware / Cyber Threat The North Korea-linked threat actor known as Lazarus Group employed its time-tested fabricated job lures to deliver a new remote access trojan called Kaolin RAT. The malware could, “aside from standard RAT functionality, change the last write timestamp of a selected file and load any received DLL binary…
Network Threats: A Step-by-Step Attack Demonstration
[ad_1] Follow this real-life network attack simulation, covering 6 steps from Initial Access to Data Exfiltration. See how attackers remain undetected with the simplest tools and why you need multiple choke points in your defense strategy. Surprisingly, most network attacks are not exceptionally sophisticated, technologically advanced, or reliant on zero-day tools that exploit edge-case vulnerabilities….
Researchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
[ad_1] Apr 24, 2024NewsroomMalware / Endpoint Security Cybersecurity researchers have discovered an ongoing attack campaign that’s leveraging phishing emails to deliver malware called SSLoad. The campaign, codenamed FROZEN#SHADOW by Securonix, also involves the deployment of Cobalt Strike and the ConnectWise ScreenConnect remote desktop software. “SSLoad is designed to stealthily infiltrate systems, gather sensitive information and…
U.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
[ad_1] Apr 24, 2024NewsroomCyber Attack / Cyber Espionage The U.S. Treasury Department’s Office of Foreign Assets Control (OFAC) on Monday sanctioned two firms and four individuals for their involvement in malicious cyber activities on behalf of the Iranian Islamic Revolutionary Guard Corps Cyber Electronic Command (IRGC-CEC) from at least 2016 to April 2021. This includes…
Major Security Flaws Expose Keystrokes of Over 1 Billion Chinese Keyboard App Users
[ad_1] Apr 24, 2024NewsroomEncryption / Mobile Security Security vulnerabilities uncovered in cloud-based pinyin keyboard apps could be exploited to reveal users’ keystrokes to nefarious actors. The findings come from the Citizen Lab, which discovered weaknesses in eight of nine apps from vendors like Baidu, Honor, iFlytek, OPPO, Samsung, Tencent, Vivo, and Xiaomi. The only vendor…
Police Chiefs Call for Solutions to Access Encrypted Data in Serious Crime Cases
[ad_1] Apr 23, 2024NewsroomEnd-to-End Encryption / Privacy European Police Chiefs said that the complementary partnership between law enforcement agencies and the technology industry is at risk due to end-to-end encryption (E2EE). They called on the industry and governments to take urgent action to ensure public safety across social media platforms. “Privacy measures currently being rolled…
Apache Cordova App Harness Targeted in Dependency Confusion Attack
[ad_1] Apr 23, 2024NewsroomSupply Chain Attack / Application Security Researchers have identified a dependency confusion vulnerability impacting an archived Apache project called Cordova App Harness. Dependency confusion attacks take place owing to the fact that package managers check the public repositories before private registries, thus allowing a threat actor to publish a malicious package with…
Learn Proactive Supply Chain Threat Hunting Techniques
[ad_1] Apr 23, 2024The Hacker NewsThreat Hunting / Software Security In the high-stakes world of cybersecurity, the battleground has shifted. Supply chain attacks have emerged as a potent threat, exploiting the intricate web of interconnected systems and third-party dependencies to breach even the most formidable defenses. But what if you could turn the tables and…