[ad_1] Oct 26, 2023NewsroomCyber Threat / Social Engineering The prolific threat actor known as Scattered Spider has been observed impersonating newly hired employees in targeted firms as a ploy to blend into normal on-hire processes and takeover accounts and breach organizations across the world. Microsoft, which disclosed the activities of the financially motivated hacking crew,…
Blog
New Safari Exploit Impacts Apple iPhones and Macs with A and M-Series CPUs
[ad_1] Oct 26, 2023NewsroomData Security / Vulnerability A group of academics has devised a novel side-channel attack dubbed iLeakage that exploits a weakness in the A- and M-series CPUs running on Apple iOS, iPadOS, and macOS devices, enabling the extraction of sensitive information from the Safari web browser. “An attacker can induce Safari to render…
The Danger of Forgotten Pixels on Websites: A New Case Study
[ad_1] Oct 26, 2023The Hacker NewsWeb Security / Data Protection While cyberattacks on websites receive much attention, there are often unaddressed risks that can lead to businesses facing lawsuits and privacy violations even in the absence of hacking incidents. A new case study highlights one of these more common cases. Download the full case study…
Quasar RAT Leverages DLL Side-Loading to Fly Under the Radar
[ad_1] Oct 23, 2023NewsroomCyberattack / Malware The open-source remote access trojan known as Quasar RAT has been observed leveraging DLL side-loading to fly under the radar and stealthily siphon data from compromised Windows hosts. “This technique capitalizes on the inherent trust these files command within the Windows environment,” Uptycs researchers Tejaswini Sandapolla and Karthickkumar Kathiresan…
1Password Detects Suspicious Activity Following Okta Support Breach
[ad_1] Oct 24, 2023NewsroomCyber Attack / Password Management Popular password management solution 1Password said it detected suspicious activity on its Okta instance on September 29 following the support system breach, but reiterated that no user data was accessed. “We immediately terminated the activity, investigated, and found no compromise of user data or other sensitive systems,…
Backdoor Implanted on Hacked Cisco Devices Modified to Evade Detection
[ad_1] Oct 24, 2023NewsroomCyber Threat / Vulnerability The backdoor implanted on Cisco devices by exploiting a pair of zero-day flaws in IOS XE software has been modified by the threat actor so as to escape visibility via previous fingerprinting methods. “Investigated network traffic to a compromised device has shown that the threat actor has upgraded…
Malvertising Campaign Targets Brazil’s PIX Payment System with GoPIX Malware
[ad_1] The popularity of Brazil’s PIX instant payment system has made it a lucrative target for threat actors looking to generate illicit profits using a new malware called GoPIX. Kaspersky, which has been tracking the active campaign since December 2022, said the attacks are pulled off using malicious ads that are served when potential victims…
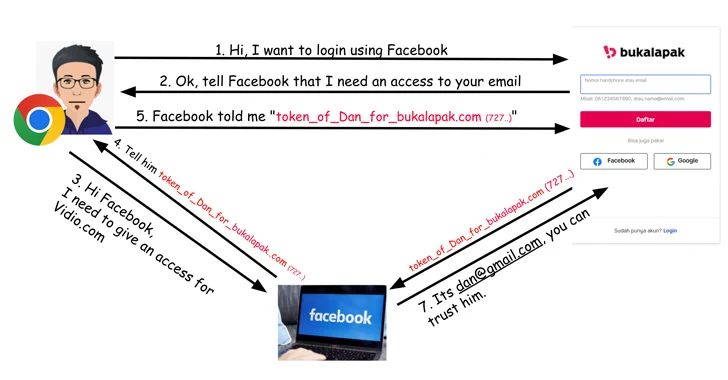
Critical OAuth Flaws Uncovered in Grammarly, Vidio, and Bukalapak Platforms
[ad_1] Oct 25, 2023Newsroom Critical security flaws have been disclosed in the Open Authorization (OAuth) implementation of popular online services such as Grammarly, Vidio, and Bukalapak, building upon previous shortcomings uncovered in Booking[.]com and Expo. The weaknesses, now addressed by the respective companies following responsible disclosure between February and April 2023, could have allowed malicious…
Nation State Hackers Exploiting Zero-Day in Roundcube Webmail Software
[ad_1] Oct 25, 2023NewsroomThreat Intelligence / Vulnerability The threat actor known as Winter Vivern has been observed exploiting a zero-day flaw in Roundcube webmail software on October 11, 2023, to harvest email messages from victims’ accounts. “Winter Vivern has stepped up its operations by using a zero-day vulnerability in Roundcube,” ESET security researcher Matthieu Faou…
How to Identify and Combat It
[ad_1] Oct 25, 2023The Hacker NewsRansomware/ Malware Threat In today’s digital landscape, around 60% of corporate data now resides in the cloud, with Amazon S3 standing as the backbone of data storage for many major corporations. Despite S3 being a secure service from a reputable provider, its pivotal role in handling vast amounts of sensitive…