[ad_1] Oct 09, 2023The Hacker NewsArtificial Intelligence / CISO In today’s rapidly evolving technological landscape, the integration of Artificial Intelligence (AI) and Large Language Models (LLMs) has become ubiquitous across various industries. This wave of innovation promises improved efficiency and performance, but lurking beneath the surface are complex vulnerabilities and unforeseen risks that demand immediate…
Blog
Cybercriminals Using EvilProxy Phishing Kit to Target Senior Executives in U.S. Firms
[ad_1] Oct 09, 2023NewsroomCredential Harvesting / Hacking Senior executives working in U.S.-based organizations are being targeted by a new phishing campaign that leverages a popular adversary-in-the-middle (AiTM) phishing toolkit named EvilProxy to conduct credential harvesting and account takeover attacks. Menlo Security said the activity started in July 2023, primarily singling out banking and financial services,…
Massive Ad Fraud Botnet Powered by Millions of Hacked Android and iOS
[ad_1] Oct 09, 2023NewsroomBotnet / Cyber Threat An ad fraud botnet dubbed PEACHPIT leveraged an army of hundreds of thousands of Android and iOS devices to generate illicit profits for the threat actors behind the scheme. The botnet is part of a larger China-based operation codenamed BADBOX, which also entails selling off-brand mobile and connected…
New ZenRAT Malware Targeting Windows Users via Fake Password Manager Software
[ad_1] Sep 27, 2023NewsroomMalware / Cyber Threat A new malware strain called ZenRAT has emerged in the wild that’s distributed via bogus installation packages of the Bitwarden password manager. “The malware is specifically targeting Windows users and will redirect people using other hosts to a benign web page,” enterprise security firm Proofpoint said in a…
New Survey Uncovers How Companies Are Confronting Data Security Challenges Head-On
[ad_1] Data security is in the headlines often, and it’s almost never for a positive reason. Major breaches, new ways to hack into an organization’s supposedly secure data, and other threats make the news because well, it’s scary — and expensive. Data breaches, ransomware and malware attacks, and other cybercrime might be pricey to prevent,…
Researchers Uncover New GPU Side-Channel Vulnerability Leaking Sensitive Data
[ad_1] Sep 27, 2023NewsroomVulnerability / Endpoint Security A novel side-channel attack called GPU.zip renders virtually all modern graphics processing units (GPU) vulnerable to information leakage. “This channel exploits an optimization that is data dependent, software transparent, and present in nearly all modern GPUs: graphical data compression,” a group of academics from the University of Texas…
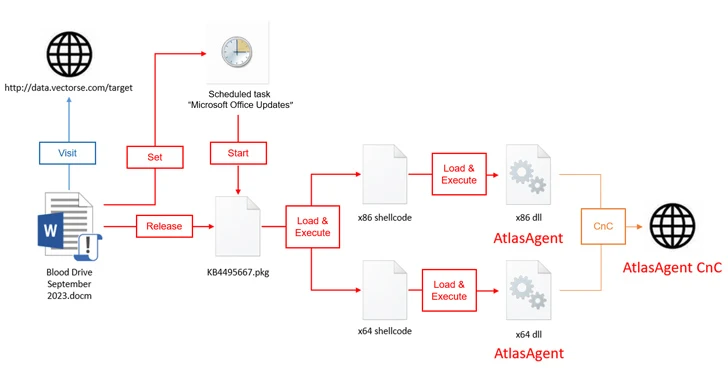
Red Cross-Themed Phishing Attacks Distributing DangerAds and AtlasAgent Backdoors
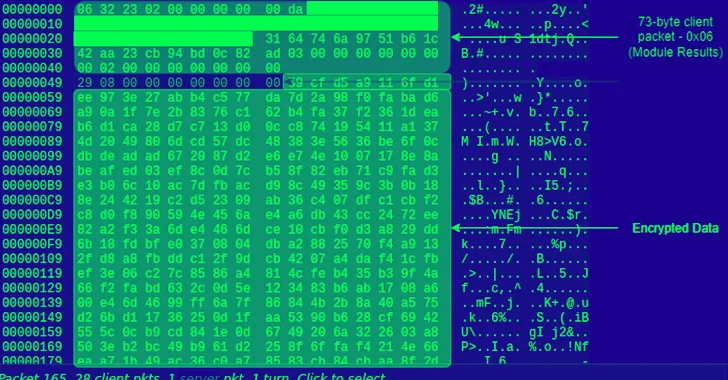
[ad_1] Sep 27, 2023NewsroomMalware / Cyber Attack A new threat actor known as AtlasCross has been observed leveraging Red Cross-themed phishing lures to deliver two previously undocumented backdoors named DangerAds and AtlasAgent. NSFOCUS Security Labs described the adversary as having a “high technical level and cautious attack attitude,” adding that “the phishing attack activity captured…
China-Linked Budworm Targeting Middle Eastern Telco and Asian Government Agencies
[ad_1] Sep 28, 2023NewsroomMalware / Cyber Threat Government and telecom entities have been subjected to a new wave of attacks by a China-linked threat actor tracked as Budworm using an updated malware toolset. The intrusions, targeting a Middle Eastern telecommunications organization and an Asian government, took place in August 2023, with the adversary deploying an…
The Dark Side of Browser Isolation – and the Next Generation Browser Security Technologies
[ad_1] Sep 28, 2023The Hacker NewsBrowser Security / Cybersecurity The landscape of browser security has undergone significant changes over the past decade. While Browser Isolation was once considered the gold standard for protecting against browser exploits and malware downloads, it has become increasingly inadequate and insecure in today’s SaaS-centric world. The limitations of Browser Isolation,…
China’s BlackTech Hacking Group Exploited Routers to Target U.S. and Japanese Companies
[ad_1] Cybersecurity agencies from Japan and the U.S. have warned of attacks mounted by a state-backed hacking group from China to stealthily tamper with branch routers and use them as jumping-off points to access the networks of various companies in the two countries. The attacks have been tied to a malicious cyber actor dubbed BlackTech…