[ad_1] Feb 04, 2025Ravie LakshmananMalware / Cryptocurrency The North Korean threat actors behind the Contagious Interview campaign have been observed delivering a collection of Apple macOS malware strains dubbed FERRET as part of a supposed job interview process. “Targets are typically asked to communicate with an interviewer through a link that throws an error message…
Category: Cyber News
Russian Cybercrime Groups Exploiting 7-Zip Flaw to Bypass Windows MotW Protections
[ad_1] Feb 04, 2025Ravie LakshmananVulnerability / Cyber Espionage A recently patched security vulnerability in the 7-Zip archiver tool was exploited in the wild to deliver the SmokeLoader malware. The flaw, CVE-2025-0411 (CVSS score: 7.0), allows remote attackers to circumvent mark-of-the-web (MotW) protections and execute arbitrary code in the context of the current user. It was…
Microsoft Patches Critical Azure AI Face Service Vulnerability with CVSS 9.9 Score
[ad_1] Feb 04, 2025The Hacker NewsVulnerability / Cloud Security Microsoft has released patches to address two Critical-rated security flaws impacting Azure AI Face Service and Microsoft Account that could allow a malicious actor to escalate their privileges under certain conditions. The flaws are listed below – CVE-2025-21396 (CVSS score: 7.5) – Microsoft Account Elevation of…
Microsoft SharePoint Connector Flaw Could’ve Enabled Credential Theft Across Power Platform
[ad_1] Feb 04, 2025Ravie LakshmananVulnerability / SharePoint Cybersecurity researchers have disclosed details of a now-patched vulnerability impacting the Microsoft SharePoint connector on Power Platform that, if successfully exploited, could allow threat actors to harvest a user’s credentials and stage follow-on attacks. This could manifest in the form of post-exploitation actions that allow the attacker to…
What Is Attack Surface Management?
[ad_1] Attack surfaces are growing faster than security teams can keep up – to stay ahead, you need to know what’s exposed and where attackers are most likely to strike. With cloud adoption dramatically increasing the ease of exposing new systems and services to the internet, prioritizing threats and managing your attack surface from an…
Now Targets 1,030 Sites and 73 Financial Institutions
[ad_1] Feb 03, 2025Ravie LakshmananFinancial Security / Malware Brazilian Windows users are the target of a campaign that delivers a banking malware known as Coyote. “Once deployed, the Coyote Banking Trojan can carry out various malicious activities, including keylogging, capturing screenshots, and displaying phishing overlays to steal sensitive credentials,” Fortinet FortiGuard Labs researcher Cara Lin…
Top Cybersecurity Threats, Tools and Tips [27 February]
[ad_1] Feb 03, 2025Ravie LakshmananCybersecurity / Recap This week, our news radar shows that every new tech idea comes with its own challenges. A hot AI tool is under close watch, law enforcement is shutting down online spots that help cybercriminals, and teams are busy fixing software bugs that could let attackers in. From better…
PyPI Introduces Archival Status to Alert Users About Unmaintained Python Packages
[ad_1] Feb 03, 2025Ravie LakshmananOpen Source / Software Security The maintainers of the Python Package Index (PyPI) registry have announced a new feature that allows package developers to archive a project as part of efforts to improve supply chain security. “Maintainers can now archive a project to let users know that the project is not…
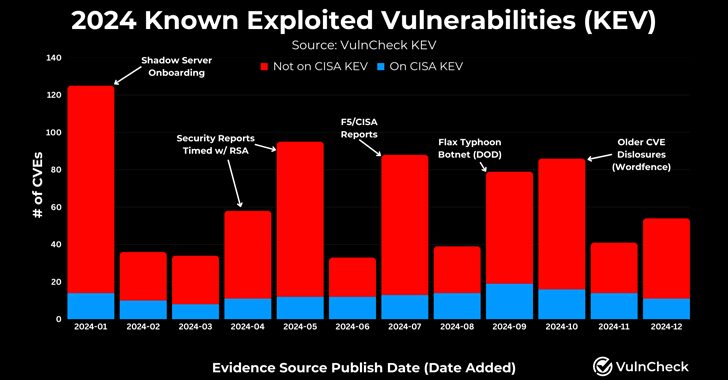
768 CVEs Exploited in 2024, Reflecting a 20% Increase from 639 in 2023
[ad_1] Feb 03, 2025Ravie LakshmananVulnerability / Network Security As many as 768 vulnerabilities with designated CVE identifiers were reported as exploited in the wild in 2024, up from 639 CVEs in 2023, registering a 20% increase year-over-year. Describing 2024 as “another banner year for threat actors targeting the exploitation of vulnerabilities,” VulnCheck said 23.6% of…
Crazy Evil Gang Targets Crypto with StealC, AMOS, and Angel Drainer Malware
[ad_1] A Russian-speaking cybercrime gang known as Crazy Evil has been linked to over 10 active social media scams that leverage a wide range of tailored lures to deceive victims and trick them into installing malware such as StealC, Atomic macOS Stealer (aka AMOS), and Angel Drainer. “Specializing in identity fraud, cryptocurrency theft, and information-stealing…