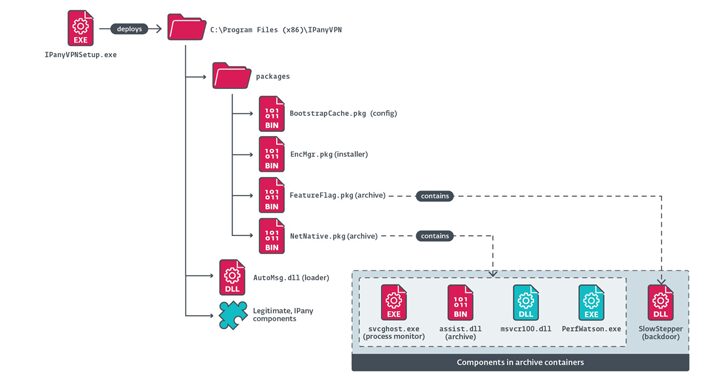
[ad_1] A previously undocumented China-aligned advanced persistent threat (APT) group named PlushDaemon has been linked to a supply chain attack targeting a South Korean virtual private network (VPN) provider in 2023, according to new findings from ESET. “The attackers replaced the legitimate installer with one that also deployed the group’s signature implant that we have…
Category: Cyber News
President Trump Pardons Silk Road Creator Ross Ulbricht After 11 Years in Prison
[ad_1] Jan 22, 2025Ravie LakshmananDark Web / Cryptocurrency U.S. President Donald Trump on Tuesday granted a “full and unconditional pardon” to Ross Ulbricht, the creator of the infamous Silk Road drug marketplace, after spending 11 years behind bars. “I just called the mother of Ross William Ulbricht to let her know that in honor of…
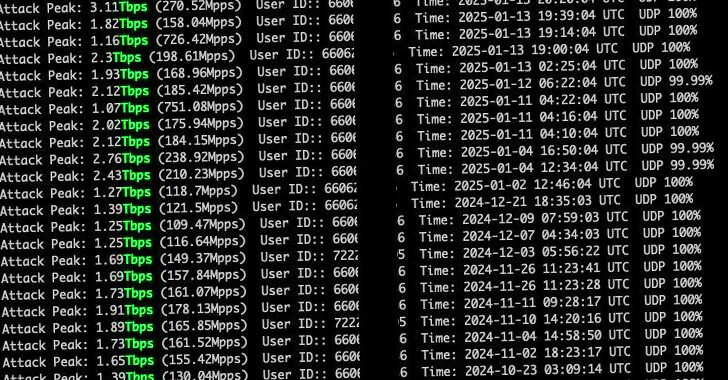
Hackers Exploit Zero-Day in cnPilot Routers to Deploy AIRASHI DDoS Botnet
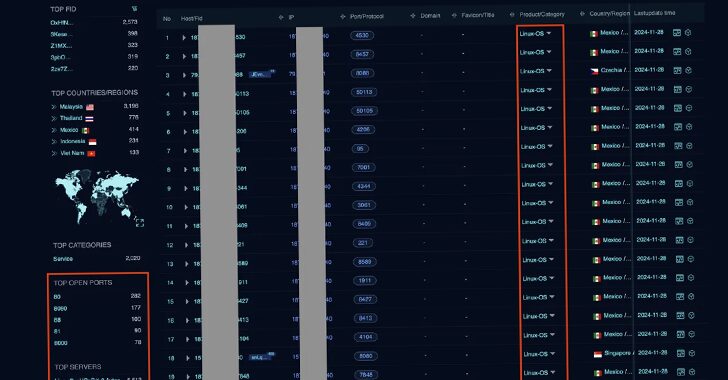
[ad_1] Threat actors are exploiting an unspecified zero-day vulnerability in Cambium Networks cnPilot routers to deploy a variant of the AISURU botnet called AIRASHI to carry out distributed denial-of-service (DDoS) attacks. According to QiAnXin XLab, the attacks have leveraged the security flaw since June 2024. Additional details about the shortcomings have been withheld to prevent…
Trump Terminates DHS Advisory Committee Memberships, Disrupting Cybersecurity Review
[ad_1] Jan 22, 2025Ravie LakshmananCybersecurity / National Security The new Trump administration has terminated all memberships of advisory committees that report to the Department of Homeland Security (DHS). “In alignment with the Department of Homeland Security’s (DHS) commitment to eliminating the misuse of resources and ensuring that DHS activities prioritize our national security, I am…
Free Risk Assessment for GenAI, Identity, Web, and SaaS Risks
[ad_1] Jan 22, 2025The Hacker NewsRisk Assessment / Browser Security As GenAI tools and SaaS platforms become a staple component in the employee toolkit, the risks associated with data exposure, identity vulnerabilities, and unmonitored browsing behavior have skyrocketed. Forward-thinking security teams are looking for security controls and strategies to address these risks, but they do…
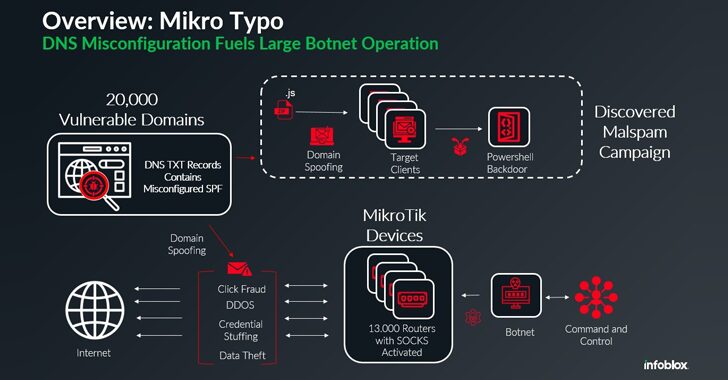
13,000 MikroTik Routers Hijacked by Botnet for Malspam and Cyberattacks
[ad_1] Jan 21, 2025Ravie LakshmananEmail Security / Botnet A global network of about 13,000 hijacked Mikrotik routers has been employed as a botnet to propagate malware via spam campaigns, the latest addition to a list of botnets powered by MikroTik devices. The activity “take[s] advantage of misconfigured DNS records to pass email protection techniques,” Infoblox…
Mirai Variant Murdoc Botnet Exploits AVTECH IP Cameras and Huawei Routers
[ad_1] Jan 21, 2025Ravie LakshmananBotnet / Vulnerability Cybersecurity researchers have warned of a new large-scale campaign that exploits security flaws in AVTECH IP cameras and Huawei HG532 routers to rope the devices into a Mirai botnet variant dubbed Murdoc Botnet. The ongoing activity “demonstrates enhanced capabilities, exploiting vulnerabilities to compromise devices and establish expansive botnet…
Setting New Standards for Visibility and Control in Penetration Testing Projects
[ad_1] Imagine receiving a penetration test report that leaves you with more questions than answers. Questions like, “Were all functionalities of the web app tested?” or ” Were there any security issues that could have been identified during testing?” often go unresolved, raising concerns about the thoroughness of the security testing. This frustration is common…
DoNot Team Linked to New Tanzeem Android Malware Targeting Intelligence Collection
[ad_1] Jan 20, 2025Ravie LakshmananAndroid / Malware The Threat actor known as DoNot Team has been linked to a new Android malware as part of highly targeted cyber attacks. The artifacts in question, named Tanzeem (meaning “organization” in Urdu) and Tanzeem Update, were spotted in October and December 2024 by cybersecurity company Cyfirma. The apps…
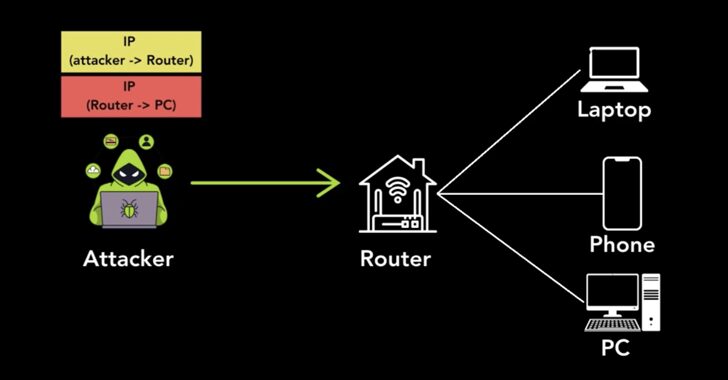
Unsecured Tunneling Protocols Expose 4.2 Million Hosts, Including VPNs and Routers
[ad_1] Jan 20, 2025Ravie LakshmananNetwork Security / Vulnerability New research has uncovered security vulnerabilities in multiple tunneling protocols that could allow attackers to perform a wide range of attacks. “Internet hosts that accept tunneling packets without verifying the sender’s identity can be hijacked to perform anonymous attacks and provide access to their networks,” Top10VPN said…