[ad_1] Jan 10, 2025Ravie LakshmananCryptomining / Malware Cybersecurity company CrowdStrike is alerting of a phishing campaign that exploits its own branding to distribute a cryptocurrency miner that’s disguised as an employee CRM application as part of a supposed recruitment process. “The attack begins with a phishing email impersonating CrowdStrike recruitment, directing recipients to a malicious…
Category: Cyber News
RedDelta Deploys PlugX Malware to Target Mongolia and Taiwan in Espionage Campaigns
[ad_1] Jan 10, 2025Ravie LakshmananCyber Espionage / Cyber Attack Mongolia, Taiwan, Myanmar, Vietnam, and Cambodia have been targeted by the China-nexus RedDelta threat actor to deliver a customized version of the PlugX backdoor between July 2023 and December 2024. “The group used lure documents themed around the 2024 Taiwanese presidential candidate Terry Gou, the Vietnamese…
Microsegmentation For all Users, Workloads and Devices by Elisity
[ad_1] Network segmentation remains a critical security requirement, yet organizations struggle with traditional approaches that demand extensive hardware investments, complex policy management, and disruptive network changes. Healthcare and manufacturing sectors face particular challenges as they integrate diverse endpoints – from legacy medical devices to IoT sensors – onto their production networks. These devices often lack…
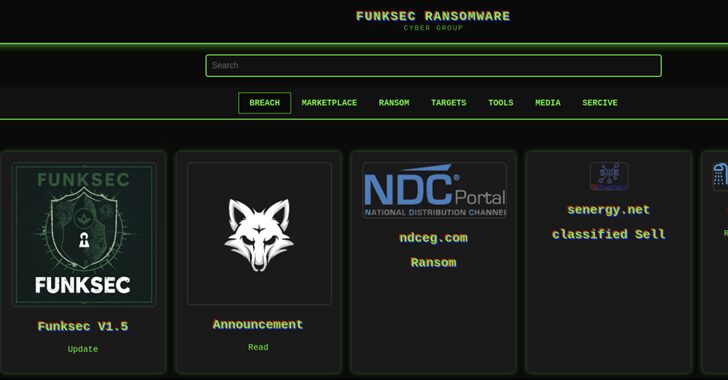
AI-Driven Ransomware FunkSec Targets 85 Victims Using Double Extortion Tactics
[ad_1] Cybersecurity researchers have shed light on a nascent artificial intelligence (AI) assisted ransomware family called FunkSec that sprang forth in late 2024, and has claimed more than 85 victims to date. “The group uses double extortion tactics, combining data theft with encryption to pressure victims into paying ransoms,” Check Point Research said in a…
Microsoft Sues Hacking Group Exploiting Azure AI for Harmful Content Creation
[ad_1] Jan 11, 2025Ravie LakshmananAI Security / Cybersecurity Microsoft has revealed that it’s pursuing legal action against a “foreign-based threat–actor group” for operating a hacking-as-a-service infrastructure to intentionally get around the safety controls of its generative artificial intelligence (AI) services and produce offensive and harmful content. The tech giant’s Digital Crimes Unit (DCU) said it…
DoJ Indicts Three Russians for Operating Crypto Mixers Used in Cybercrime Laundering
[ad_1] Jan 11, 2025Ravie LakshmananFinancial Crime / Cryptocurrency The U.S. Department of Justice (DoJ) on Friday indicted three Russian nationals for their alleged involvement in operating the cryptocurrency mixing services Blender.io and Sinbad.io. Roman Vitalyevich Ostapenko and Alexander Evgenievich Oleynik were arrested on December 1, 2024, in coordination with the Netherlands’ Financial Intelligence and Investigative…
A Practical Guide for MSPs
[ad_1] Cybersecurity reporting is a critical yet often overlooked opportunity for service providers managing cybersecurity for their clients, and specifically for virtual Chief Information Security Officers (vCISOs). While reporting is seen as a requirement for tracking cybersecurity progress, it often becomes bogged down with technical jargon, complex data, and disconnected spreadsheets that fail to resonate…
Google Project Zero Researcher Uncovers Zero-Click Exploit Targeting Samsung Devices
[ad_1] Jan 10, 2025Ravie LakshmananCybersecurity / Android Cybersecurity researchers have detailed a now-patched security flaw impacting Monkey’s Audio (APE) decoder on Samsung smartphones that could lead to code execution. The high-severity vulnerability, tracked as CVE-2024-49415 (CVSS score: 8.1), affects Samsung devices running Android versions 12, 13, and 14. “Out-of-bounds write in libsaped.so prior to SMR…
How Reco Discovers Shadow AI in SaaS
[ad_1] As SaaS providers race to integrate AI into their product offerings to stay competitive and relevant, a new challenge has emerged in the world of AI: shadow AI. Shadow AI refers to the unauthorized use of AI tools and copilots at organizations. For example, a developer using ChatGPT to assist with writing code, a…
Major Vulnerabilities Patched in SonicWall, Palo Alto Expedition, and Aviatrix Controllers
[ad_1] Jan 09, 2025Ravie LakshmananVulnerability / Endpoint Security Palo Alto Networks has released software patches to address several security flaws in its Expedition migration tool, including a high-severity bug that an authenticated attacker could exploit to access sensitive data. “Multiple vulnerabilities in the Palo Alto Networks Expedition migration tool enable an attacker to read Expedition…